Multi-agent system networking guide: 86.7% failure fix
Orchestrating secure, real-time communication across dozens or hundreds of autonomous agents is one of the hardest problems in distributed AI engineering. Agents need to find each other, verify identity, exchange data, and recover from failures, all without a central coordinator slowing things down or becoming a single point of failure. This guide walks you through the specific networking challenges, architectural requirements, and step-by-step configuration decisions that determine whether your multi-agent system (MAS) succeeds or collapses under load. You will leave with a clear, actionable framework for building secure, scalable agent networks in production.
Table of Contents
- Understanding multi-agent networking challenges
- Requirements and architecture for secure MAS networking
- Step-by-step: Building and configuring a secure multi-agent network
- Testing, troubleshooting, and benchmarking MAS networks
- Connect your multi-agent systems with enterprise-grade networking
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Decentralized outperforms | Decentralized MAS networking yields better scalability and privacy, though at higher coordination complexity. |
| Protocol selection matters | Choosing the right protocol can affect completion time by up to 36 percent and impact reliability. |
| Test before deploying | Benchmark your MAS network with tools like AgentsNet and COMMA to identify issues before full rollout. |
| Minimal communication is key | Clear roles and minimal overhead help reduce errors and coordination failures in multi-agent networks. |
Understanding multi-agent networking challenges
Decentralized agent networks operate under constraints that traditional client-server architectures simply were not designed to handle. Agents are dynamic. They join and leave the network, change roles, and must coordinate without a trusted central authority. That combination creates three core requirements: trust establishment between unknown peers, privacy for sensitive data in transit, and fault-tolerance when nodes drop unexpectedly.
Common coordination patterns in MAS include:
- Request-response: One agent queries another directly. Simple, but brittle at scale.
- Publish-subscribe (pub-sub): Agents broadcast state changes to subscribers. Efficient, but requires a reliable message bus.
- Blackboard systems: Agents read and write to a shared data structure. Powerful for complex tasks, but introduces contention and consistency challenges.
Each pattern has edge cases that can cascade into system-wide failures. Research on MAS failure rates shows that miscommunication, strategy coordination failures, and verification issues produce failure rates between 41% and 86.7% across state-of-the-art systems tested on benchmarks like SWE-Bench and GAIA.
“Communication patterns include request-response, pub-sub, and blackboard systems. Edge cases involve strategy coordination failures, miscommunication, conflicting objectives, and verification issues, with failure rates reaching 86.7% in MAS.”
Those numbers are not theoretical. They represent real production-grade systems failing on real tasks. Understanding secure agent communication principles from the start is what separates a resilient MAS from one that fails silently. If you want to see how fast a basic network can come together, a quick MAS network setup gives you a working baseline in minutes.
Requirements and architecture for secure MAS networking
With the challenges and risks in mind, assemble the baseline requirements and explore the architectural options available to you.
Before writing a single line of agent code, confirm you have these components in place:
- Agent runtime: A process manager or container orchestrator (Docker, Kubernetes, or a lightweight Go binary) that can restart agents on failure.
- Networking stack: Support for NAT traversal, encrypted tunnels, and persistent virtual addresses so agents can reach each other across clouds and regions.
- Security modules: Mutual TLS or equivalent for peer authentication, plus key rotation and revocation capabilities.
- Capability discovery: A mechanism for agents to advertise what they can do and find peers with matching capabilities.
- Consensus or coordination layer: Depending on your task type, you may need a lightweight consensus protocol or a shared ledger.
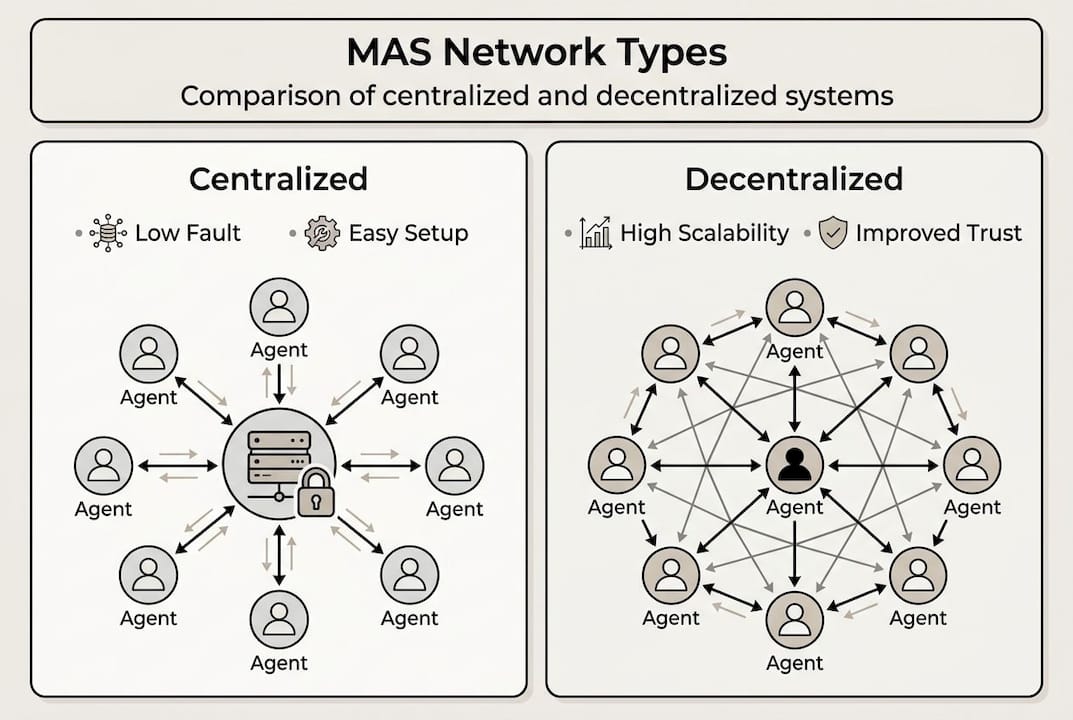
The architectural choice between centralized and decentralized coordination has major implications. Here is a direct comparison:
| Dimension | Centralized (e.g., MCP broker) | Decentralized (e.g., Symphony) |
|---|---|---|
| Fault-tolerance | Low (single point of failure) | High (no central coordinator) |
| Scalability | Limited by broker capacity | Scales with agent count |
| Privacy | Data flows through central node | Data stays at edge nodes |
| Setup complexity | Lower | Higher |
| Trust model | Implicit (trust the broker) | Explicit (peer verification) |
Decentralized approaches like the Symphony framework use blockchain for trust-aware communication, federated learning for path planning, and ledger-based capability discovery to deliver scalability and privacy without central orchestrators. For teams building private MAS networks inside an organization, this model also reduces the risk of internal data leakage.

The MCP protocol sits in a middle ground: it standardizes how agents connect to tools and data sources, but still benefits from a decentralized transport layer underneath.
Pro Tip: Start with a hybrid model. Use MCP for tool and resource integration, and layer a decentralized peer-to-peer transport like Pilot Protocol underneath for agent-to-agent communication. This gives you standardized interfaces without sacrificing fault-tolerance.
Step-by-step: Building and configuring a secure multi-agent network
After gathering your requirements, move to step-by-step configuration and integration based on your chosen framework.
- Plan your agent topology. Map out which agents need to communicate directly, which can use pub-sub, and which require shared state. Document role boundaries clearly before writing code.
- Choose your communication protocol. MCP details show it uses JSON-RPC to standardize AI model connections to tools, data sources, and services, solving the M×N integration problem with primitives like tools, resources, and prompts. For direct agent-to-agent messaging, evaluate whether request-response or pub-sub fits your latency requirements.
- Set up your networking layer. Deploy virtual addresses and encrypted tunnels for each agent. Configure NAT traversal so agents behind firewalls or in different cloud regions can reach each other without manual port forwarding.
- Establish mutual trust. Use token-gated join flows or certificate-based authentication so only authorized agents can enter the network. Rotate keys on a schedule.
- Integrate capability discovery. Register each agent’s capabilities at startup. Use a ledger or distributed registry so agents can find peers dynamically without hardcoded addresses.
- Test communication patterns in isolation. Before running full workflows, verify that each pattern (request-response, pub-sub, blackboard) works correctly between two agents. Catch serialization and timeout bugs early.
- Automate deployment. Wire agent startup and network registration into your CI/CD pipeline. Check out agent networking automation for a one-command deployment example.
Here is a quick protocol comparison to guide your selection:
| Protocol | Best for | Overhead | Fault-tolerance |
|---|---|---|---|
| MCP (JSON-RPC) | Tool and resource integration | Low | Medium |
| Symphony (ledger-based) | Large-scale decentralized MAS | Medium | High |
| HTTP overlay | Legacy system integration | Medium | Medium |
| UDP overlay | Low-latency real-time tasks | Very low | Low |
Understanding the full agent network stack helps you make these protocol decisions with confidence rather than guesswork.
Pro Tip: Keep agent roles narrow. An agent that does one thing well is easier to monitor, replace, and scale than a generalist agent. Role clarity also reduces the coordination overhead that drives up failure rates.
Testing, troubleshooting, and benchmarking MAS networks
Once your MAS network is in place, rigorously validate scalability, reliability, and robustness through real-world testing.
Three benchmarks are worth knowing:
- AgentsNet: Tests scalable coordination on graph problems with up to 100+ agents, making it ideal for evaluating how your network handles growing agent counts.
- COMMA: Evaluates multimodal collaboration, useful if your agents exchange images, audio, or structured data alongside text.
- ProtocolBench: Directly compares communication protocols and has shown up to 36% task time variance depending on protocol choice. That is not a minor difference. It means the wrong protocol can make your system a third slower before you write a single line of business logic.
Common issues to debug during testing:
- Message loss: Check buffer sizes and confirm your transport layer retransmits on failure.
- Agent discovery failures: Verify that capability registrations are propagating correctly across all nodes.
- Latency spikes: Profile your serialization layer. JSON is readable but slow at high message volumes. Consider MessagePack or Protocol Buffers for hot paths.
- Split-brain scenarios: If agents disagree on shared state, your consensus layer needs tuning. Add explicit conflict resolution logic.
- Authentication timeouts: Token expiry during long-running tasks can silently drop connections. Build in token refresh logic.
For reliability checklists, track these metrics continuously:
- Message delivery rate (target: above 99.9%)
- Agent reconnection time after failure (target: under 2 seconds)
- End-to-end task completion rate across your benchmark suite
- Protocol overhead as a percentage of total task time
Research on MAS productivity gains confirms that well-architected multi-agent systems outperform single-agent approaches on complex tasks, but only when the communication layer is reliable. For teams scaling agents to thousands of instances, these benchmarks become essential gates before production rollout. If you are building a system that self-organizes into swarms, add chaos testing to your suite. Kill random agents mid-task and verify the swarm recovers without human intervention. You can also review HTTP vs UDP for MAS to make data-driven transport decisions based on your specific workload profile.
Connect your multi-agent systems with enterprise-grade networking
You have mapped the failure modes, selected your architecture, configured your protocols, and validated your network under load. The next step is making sure your production deployment has the networking infrastructure to support it all reliably.

Pilot Protocol gives your agents persistent virtual addresses, encrypted peer-to-peer tunnels, NAT traversal, and mutual trust establishment out of the box. It wraps existing protocols like HTTP, gRPC, and SSH inside its overlay, so you can integrate with legacy systems without rebuilding your stack. Whether you are running a two-agent pipeline or a fleet of thousands across multiple clouds, Pilot Protocol handles the networking layer so your team can focus on agent logic. Explore the platform, try the CLI or Python and Go SDKs, and get your first private agent network running today.
Frequently asked questions
What is the main benefit of decentralized MAS networking?
Decentralized MAS networking improves scalability, privacy, and fault-tolerance by removing the central coordinator. Frameworks like Symphony use ledger-based discovery and federated learning to keep agents coordinated without a single point of failure.
Which protocols are recommended for agent-to-agent communication?
Protocols like MCP, Symphony, and hybrid HTTP/UDP overlays are commonly recommended. MCP standardizes tool and resource connections using JSON-RPC, while UDP overlays reduce latency for real-time agent messaging.
How do you benchmark MAS network scalability?
Use AgentsNet, COMMA, and ProtocolBench to evaluate scalability, multimodal collaboration, and protocol efficiency. These frameworks give you quantitative data on coordination overhead and task completion rates.
What are typical failure rates in MAS communication?
Failure rates range from 41% to 86.7% in state-of-the-art MAS under benchmark testing. Addressing trust, verification, and protocol selection early in your architecture reduces these rates significantly.


