Encrypted data exchange for decentralized AI systems
Encrypted data exchange for decentralized AI systems

TL;DR:
- Misconfigured keystores or protocols can expose sensitive AI agent data across networks and cloud environments. Ensuring robust encryption involves addressing multiple exposure surfaces, including metadata, and selecting appropriate protocols like Signal or Noise for decentralized, peer-to-peer, or asynchronous communication. Implementing strict key management, regular rotation, and thorough testing prevents operational failures and strengthens security against both current and future threats.
A single misconfigured key store or a misapplied protocol can expose sensitive AI agent data across every node in your network, from multi-cloud deployments to peer-to-peer (P2P) clusters. As AI agents increasingly operate autonomously across untrusted domains, the consequences of getting encryption wrong compound fast. This guide walks you through the full picture: the threat landscape, the right protocols and tooling, a step-by-step implementation flow, and how to validate your setup before it fails in production.
Table of Contents
- Understanding the risks: Why encryption is essential in decentralized AI
- Getting started: Requirements, protocols, and tools overview
- Step-by-step: Implementing encrypted data exchange protocols
- Testing, validation, and common pitfalls to avoid
- What most get wrong about encrypted data exchange for autonomous AI
- Take AI agent security further with Pilot Protocol
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Encryption is not optional | End-to-end encryption is essential to protect AI agent communication across decentralized or multi-cloud systems. |
| Key management is critical | Most data leaks trace back to poor key generation, storage, or rotation practices. |
| Choose protocols wisely | Signal, Noise, and mTLS serve specific scenarios; match your protocol to agent or cloud needs. |
| Test and audit rigorously | Automation and routine checks for nonce misuse and misconfigurations prevent the majority of breaches. |
| Plan for metadata exposure | Even perfect encryption does not hide metadata; minimize logs and external persistence for robust privacy. |
Understanding the risks: Why encryption is essential in decentralized AI
Encryption in decentralized AI is not a single switch you flip. It covers at least three distinct exposure surfaces, and each requires a separate strategy.
Data-in-transit is what TLS protects. It secures the channel between two endpoints for the duration of a session. Data-at-rest requires separate controls at the storage layer. Metadata — who communicated with whom, when, how frequently, and from which network location — is the surface most developers ignore.
E2EE protects content but not metadata (who, when, where). TLS protects transit only, not at-rest or logged data.
In practice, this means a fully TLS-encrypted channel between two agents can still leak sensitive orchestration patterns through cloud access logs, message queue metadata, or timing correlations. Real-world incidents have confirmed this. The 2022 Signal metadata analysis demonstrated that even with perfect content encryption, traffic analysis against unprotected metadata can reconstruct social graphs and agent relationships with high accuracy. For autonomous AI systems communicating across cloud boundaries, metadata exposure is not a theoretical risk.
Standard HTTPS and TLS work well for client-server models. They are not sufficient for decentralized AI agents because:
- Agents operate peer-to-peer without a trusted central authority to issue or validate certificates.
- Agent identity must be cryptographically verifiable across network boundaries, not just within a single certificate authority’s domain.
- Sessions are often asynchronous. An agent may go offline for extended periods, generating messages that must be decryptable only when the recipient comes back online.
- Cloud-persisted logs and message broker state can expose communication patterns even after the session keys are deleted.
This is why private discovery in agent networks is a foundational concern, not an optional hardening step. Before an agent can exchange encrypted data, it must find its peer without leaking intent or identity in the process.
Having established why robust encryption is non-negotiable for decentralized AI agents, let’s examine the foundation: what you’ll need before securely exchanging data.
Getting started: Requirements, protocols, and tools overview
Before you write a single line of implementation code, map your requirements across three dimensions: protocol fit, identity model, and deployment context.
Core protocols at a glance
| Protocol | Best for | Key primitive | Forward secrecy |
|---|---|---|---|
| Signal (X3DH + Double Ratchet) | Asynchronous agent messaging | X25519, Ed25519 | Yes |
| Noise (XX, IK patterns) | P2P session setup, microservices | X25519, ChaCha20 | Yes |
| mTLS | Cloud service-to-service | RSA/ECDSA certs | Partial |
| Envelope encryption + KMS | Cloud storage, data at rest | AES-256-GCM + KMS | Via rotation |
| Libsodium (crypto_box/secretbox) | General purpose AEAD | Curve25519 + XSalsa20 | Manual |
Identity layers
For autonomous agents, simple API keys or bearer tokens are not adequate. You need cryptographic identity that can be verified without a central registry:
- W3C DIDs (Decentralized Identifiers): Self-sovereign identifiers anchored on a ledger or content-addressed store, enabling agents to prove identity without a certificate authority.
- ZKP (Zero-Knowledge Proofs): Allow an agent to prove membership or authorization without revealing the underlying credential.
- PQC (Post-Quantum Cryptography): NIST-standardized algorithms like ML-KEM (Kyber) and ML-DSA (Dilithium) are now production-ready and should be evaluated for any long-lived agent deployment.
Libraries and cloud tooling
Key open-source libraries for your stack:
- libsodium: Authenticated encryption primitives like "crypto_secretbox
(XSalsa20-Poly1305) andcrypto_box` (Curve25519 + XSalsa20-Poly1305). It handles nonce generation and padding automatically. - libp2p: Full P2P networking stack with built-in Noise protocol support.
- noise-c / noise-go: Lightweight Noise Protocol implementations for embedded or Go-based agents.
- tink: Google’s multi-language crypto library with key management primitives built in.
For enterprise and cloud contexts, envelope encryption via KMS is the standard. You encrypt data with a Data Encryption Key (DEK), then encrypt the DEK with a Key Encryption Key (KEK) managed by AWS SSE-KMS, Azure Key Vault, or GCP CMEK. Each provider also offers customer-managed key options (SSE-C, CSEK) for stronger tenant isolation. Service-to-service communication in these environments typically uses mTLS with certificates provisioned by your internal PKI.
You can find a practical primer on X25519 + AES-GCM encryption and a broader overview of decentralized communication protocols worth reviewing before finalizing your stack.
Pro Tip: When choosing primitives, favor libraries with secure defaults. Libsodium’s crypto_box_easy generates a random nonce for every message automatically. Do not build your own nonce scheme. One reuse breaks confidentiality entirely.
For multi-cloud agent network security, you will typically layer mTLS between services with envelope encryption at the storage layer and Noise or Signal-derived protocols for agent-to-agent P2P channels.
With your requirements identified and the right tools in hand, it’s time to walk through step-by-step encrypted data exchange implementation for decentralized agents and multi-cloud systems.
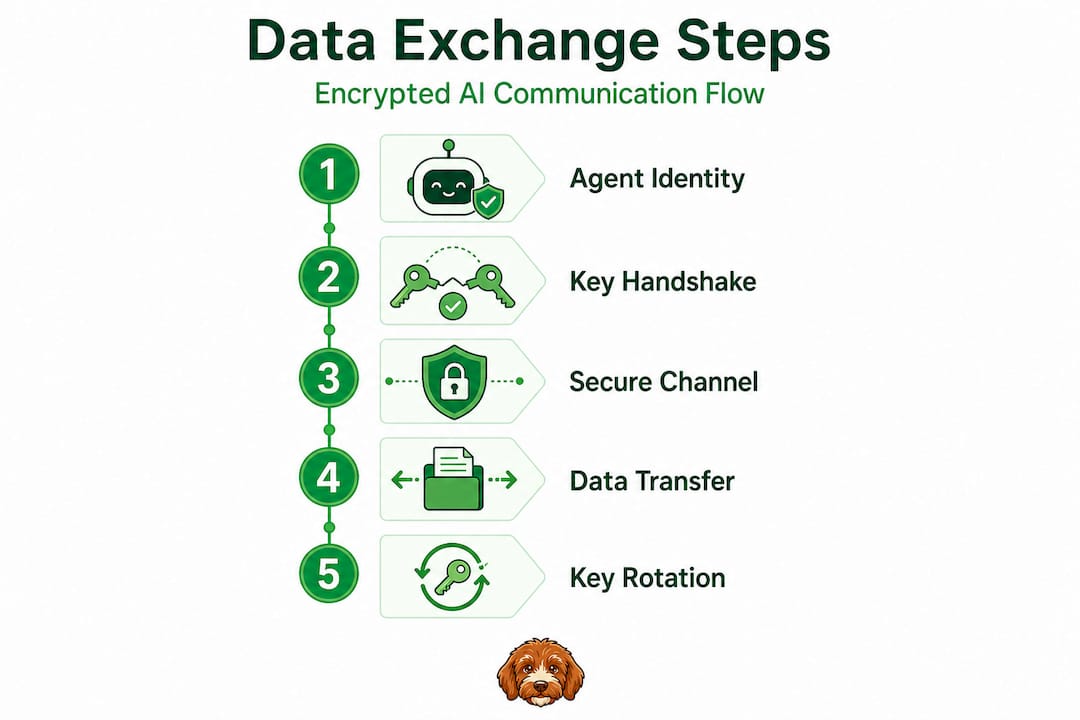
Step-by-step: Implementing encrypted data exchange protocols
1. Establish agent identity
Start with cryptographic identity before you set up any channel. Use Ed25519 key pairs for signing and X25519 key pairs for key exchange. Generate both on-device and never export the private component. If you are using DIDs, publish the public keys to your DID document. DIAP for agent identity uses IPFS/IPNS for DID anchoring, ZKPs for ownership proofs, and Libp2p GossipSub plus Iroh QUIC for the actual P2P data exchange layer.
2. Select your handshake pattern
For P2P agents that have each other’s public keys in advance, use the Noise IK pattern. This completes the handshake in 1.5 round trips and provides mutual authentication immediately. The Noise Protocol Framework enables customizable handshake patterns with DH key exchange using X25519, combined with AEAD ciphers like ChaCha20-Poly1305. WireGuard and libp2p both rely on Noise for this reason.
For agents that must discover each other without prior key knowledge, use Noise XX. It takes one full round trip more but supports mutual key exchange from scratch.
For asynchronous agent messaging (agent A sends while agent B is offline), use the Signal Protocol. Signal uses X3DH for initial key agreement and the Double Ratchet algorithm for forward secrecy and post-compromise security. This powers E2EE in Signal and WhatsApp and is well-suited to autonomous AI agents that communicate in bursts.
3. Key exchange and session setup
- Agent A fetches Agent B’s DID document and extracts the X25519 public key.
- Agent A performs an ephemeral DH exchange (X3DH or Noise IK) to derive a shared session key.
- Both agents derive a symmetric key using HKDF (HMAC-based Key Derivation Function) from the DH output.
- All subsequent messages are encrypted with AES-256-GCM or ChaCha20-Poly1305 using the derived key.
- The Double Ratchet advances the key state on every message, ensuring forward secrecy.
4. Cloud service encryption flow
- Generate a DEK (128 or 256-bit AES key) per data object or session.
- Encrypt the payload locally with the DEK using AES-256-GCM.
- Submit the DEK to your KMS (AWS KMS, Azure Key Vault, or GCP Cloud KMS) for wrapping with the KEK.
- Store the encrypted DEK alongside the ciphertext. The plaintext DEK never persists.
- For retrieval, call KMS to unwrap the DEK, decrypt locally, then discard the DEK from memory.
| Use case | Recommended protocol | Identity model | Notes |
|---|---|---|---|
| Async agent messaging | Signal (X3DH + Double Ratchet) | DID + Ed25519 | Best for offline agents |
| P2P session, known peers | Noise IK | X25519 pub keys | Fastest handshake |
| P2P session, unknown peers | Noise XX | TOFU or PKI | Full mutual auth |
| Cloud service-to-service | mTLS | PKI certs | Integrate with service mesh |
| Cloud data at rest | Envelope encryption + KMS | KMS role/policy | CMEK for tenant isolation |
Pro Tip: If your agents frequently go offline, implement asynchronous ratcheting. Pre-generate a batch of one-time prekeys and publish them to your DID document or a prekey server. Agents can then initiate sessions even when the peer is unreachable, and the ratchet advances correctly once the peer reconnects.
You can explore deeper context on protocols for distributed AI, trustless security protocols, and the full P2P AI system security checklist to validate your architecture decisions.
Now that your encrypted channel is set up, let’s review crucial steps to avoid common mistakes and catch misconfigurations before they undermine your security.
Testing, validation, and common pitfalls to avoid
Even a correctly chosen protocol fails if the implementation has gaps. Key management failures are the primary cause of E2EE breakdowns in production. Use Curve25519 or Ed25519 for identity keys, and never store private keys off-device or in shared secret management systems accessible to multiple agents.
A striking metric from production environments: 68% of cloud deployments had encryption exposure events in 2024 due to misconfiguration, even when TLS 1.3 was in use. Kafka TLS 1.3 with Vault-managed mTLS achieves 98% of unencrypted throughput at 10GB scale, meaning strong encryption has essentially zero performance cost at this point. The problem is almost never the protocol. It is the configuration around it.
Metadata exposure through logs, cloud audit trails, and persistent message queues can outlive your session keys by months or years. Treat log retention policy as a security control, not just an ops concern.
Testing checklist
Run these validations before promoting any agent network to production:
- Nonce uniqueness: Verify that no nonce is reused across any two messages using the same key. Use deterministic test vectors or fuzz your nonce generation.
- Offline agent scenarios: Simulate an agent going offline mid-session and verify that messages queued during the downtime decrypt correctly when the agent reconnects, without ratchet state corruption.
- KMS audit log review: Pull your KMS audit logs and confirm that DEK access follows the expected pattern. Unexpected decryption calls are a strong signal of a compromised agent or credential.
- Certificate and key rotation: Rotate all long-lived keys on a schedule (90 days or less for identity keys) and verify that agents renegotiate channels automatically after rotation.
- Protocol downgrade attacks: Confirm that your Noise or mTLS configuration rejects any attempt to negotiate a weaker cipher suite or handshake pattern.
- Metadata audit: Review cloud access logs, message broker retention policies, and any observability tooling that might be capturing agent communication patterns.
Common mistakes to avoid:
- Storing private keys in environment variables or shared secret stores accessible by multiple services.
- Using deterministic or counter-based nonces without collision-resistance guarantees.
- Assuming that cloud-native TLS covers your agent-to-agent P2P channels (it does not).
- Skipping mTLS between internal microservices because the network is “private.”
Pro Tip: Automate nonce and protocol version validation in your CI/CD pipeline. Write a test that sends two messages with the same key and nonce, and assert that your implementation rejects or flags the second. This catches regressions before they reach production.
For a broader view on multi-cloud networking strategies, including cross-region encryption and policy management, those resources are worth adding to your review checklist.
What most get wrong about encrypted data exchange for autonomous AI
The most common mistake is treating encryption as a single implementation event rather than an ongoing operational discipline. Teams integrate TLS, check the box, and move on. This works for a static web application. It fails for autonomous AI agent fleets.
Here is what actually goes wrong. Session keys expire but agent identity keys do not rotate. Metadata accumulates in cloud logs while the team focuses only on payload encryption. Asynchronous agents generate ratchet state that is never audited for consistency. Cross-cloud channels get mTLS while P2P agent connections rely on nothing more than API key auth.
The operational risks are the ones that matter most: automated key rotation that fails silently, agent-specific identity that gets conflated with service account identity, and recovery paths from compromise that were never designed or tested. Most practical guidance ignores offline and asynchronous agents entirely. Yet these are the agents doing the most sensitive work in modern AI workloads, running inference tasks overnight, coordinating across cloud regions, exchanging model weights and proprietary prompts.
Zero-persistence designs are the real differentiator. If your agent communication leaves no persistent state, there is nothing to exfiltrate after the fact. Combine this with DID-based identity, ZKP-based authorization, and PQC-ready key exchange, and you have an architecture that can survive both current and near-future adversaries.
Post-quantum readiness is not a future concern. Harvest-now-decrypt-later attacks are already occurring, where adversaries capture encrypted traffic today to decrypt it once quantum computers mature. Any data with a sensitivity horizon longer than five years should be protected with PQC algorithms today.
Treat encrypted data exchange for networking for distributed AI as an evolving discipline. Schedule protocol reviews at least annually, track NIST PQC standardization updates, and build your agent identity architecture to support algorithm agility from the start.
Take AI agent security further with Pilot Protocol
If you are building autonomous agent networks that need secure, direct P2P communication across cloud regions and untrusted networks, Pilot Protocol is built for exactly this problem.

Pilot Protocol provides virtual addresses, encrypted tunnels, and NAT traversal for AI agents and distributed systems, removing the need for centralized message brokers or exposed endpoints. You can explore the pilot protocol research behind the platform, review specific P2P solutions for AI agents including identity, trust establishment, and secure channel setup, or visit the Pilot Protocol platform directly to start building agent networks that are secure by design.
Frequently asked questions
What protocol should I use for autonomous agent communication?
The Noise Protocol Framework with X25519 DH and ChaCha20-Poly1305 works well for P2P agent sessions, while Signal with X3DH and Double Ratchet is the right choice for asynchronous or offline-capable agents. Both can be paired with DID-based identity and ZKP authorization for decentralized deployments.
How do I manage keys securely for encrypted data exchange?
Always generate keys on-device, use Curve25519 or Ed25519, and never store private keys on shared storage. Key management failures are the leading cause of E2EE breakdowns, so rotate and audit identity keys on a 90-day or shorter schedule.
Does end-to-end encryption protect metadata?
No. E2EE protects content but leaves metadata such as sender identity, receiver identity, timing, and frequency fully exposed. You must address metadata protection separately through log controls, zero-persistence designs, and network-layer privacy.
What is the best practice for cloud-based encrypted data exchange?
Use envelope encryption with KMS for data at rest, with AWS SSE-KMS, Azure Key Vault, or GCP CMEK for key management, and enforce mutual TLS between all services. Never persist plaintext DEKs.
How can I prevent nonce reuse in my implementation?
Use libraries like libsodium that handle randomized nonces automatically per message rather than implementing your own nonce scheme. Also add automated tests in your CI pipeline that assert nonce uniqueness across all encrypted messages.