
Securing AI agent networks in multi-cloud environments
Securing AI agent networks in multi-cloud environments

TL;DR:
- Multi-cloud agent networks face expanded attack surfaces, increasing risks of credential theft and lateral movement.
- Decentralized identifiers and verifiable credentials build scalable, trustless security for autonomous agents.
- Continuous monitoring, smart contracts, and real-time defense engines are vital for maintaining security resilience.
Two autonomous agents running across separate cloud providers attempt to share sensitive inference results. One agent’s credentials were silently compromised three hops back. Now every downstream decision is tainted. This is not a hypothetical edge case. It is the reality facing teams deploying distributed agent fleets today. Multi-cloud topologies introduce attack surfaces that traditional security models were never designed to handle. This guide walks you through the threat landscape, identity frameworks, implementation steps, and monitoring practices you need to build genuinely secure AI agent communications across decentralized environments.
Table of Contents
- Understanding the threat landscape for AI agent networks
- Building secure foundations: Identity, access, and trust frameworks
- Step-by-step: Implementing blockchain-anchored agent communication
- Verification and monitoring: Auditing agent security in production
- Our take: Moving beyond legacy paradigms for AI network security
- Next steps: Secure your AI agent network with the right infrastructure
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Decentralized identity critical | DIDs and Verifiable Credentials dramatically reduce impersonation risks for AI agent communications. |
| Blockchains anchor trust | Anchoring agent interactions and access control on blockchain stops most advanced attack vectors. |
| Automated defense matters | Tools like Defense Orchestration Engine and agent-based vulnerability testing catch threats faster than most humans. |
| Zero Trust is essential | Continuous authentication and context-aware policies are key to secure distributed agent networks. |
Understanding the threat landscape for AI agent networks
Before you can defend your agent network, you need to know what you are defending against. Multi-cloud and decentralized deployments expand the attack surface in ways that catch many teams off guard. Agents communicate across region boundaries, cloud providers, and trust domains, and each hop is a potential entry point.
The most common attack vectors targeting agent-based systems include:
- Man-in-the-middle attacks: An attacker intercepts messages between agents, reads or modifies payloads, and forwards them without detection.
- Credential compromise: Stolen API keys, tokens, or certificates allow attackers to impersonate legitimate agents.
- Privacy attacks: Inference attacks extract sensitive data from agent outputs, even when the underlying data is not directly exposed.
- Lateral movement: Once inside one node, an attacker pivots across the network by exploiting implicit trust between agents.
The networking challenges in these environments grow more complex as you add clouds, regions, and agent roles. Each new integration point is a potential gap.
What makes this especially difficult is that AI agents are increasingly capable on both sides of the security equation. The ARTEMIS benchmark reveals that AI agents can outperform many human testers at vulnerability discovery, achieving high true positive rates. But that same capability is available to attackers. Depending on the attack type, automated exploits succeed at rates as high as 88%.
Key insight: Your agent network is only as secure as its weakest trust boundary. In multi-cloud environments, those boundaries multiply fast.
Growing topology complexity also increases lateral movement risk. An agent compromised in a staging environment can become a pivot point into production if trust relationships are not scoped and verified continuously. With the risks understood, the next step is to prepare your environment for robust security.
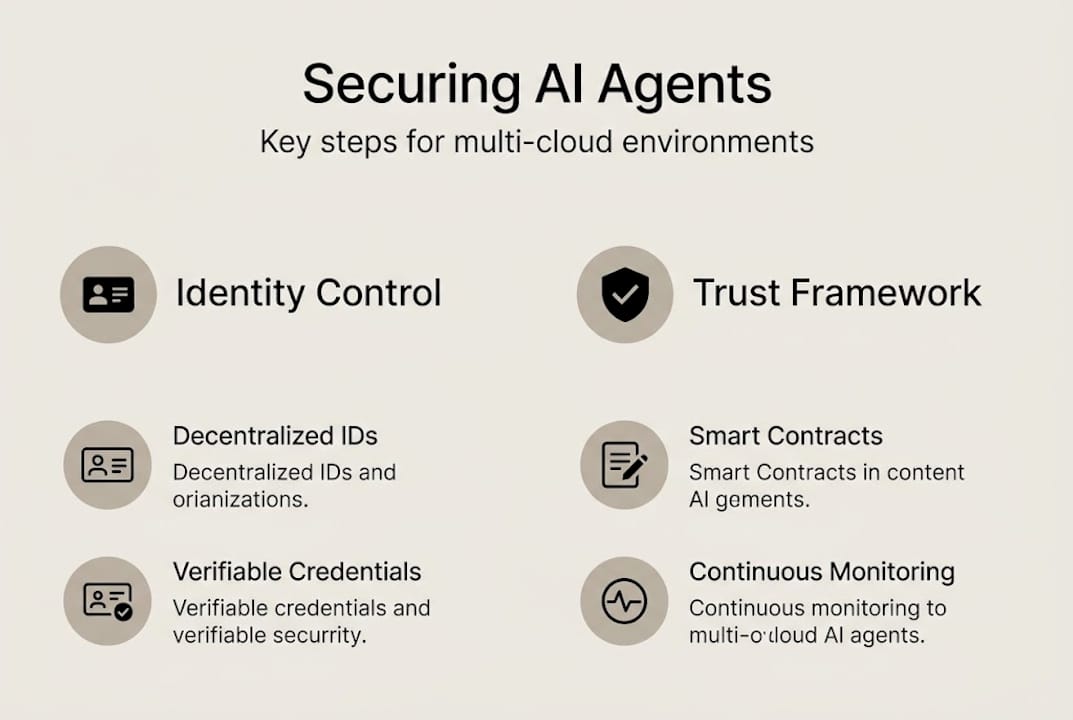
Building secure foundations: Identity, access, and trust frameworks
Legacy identity models were built for human users and static services. They were not designed for thousands of short-lived, autonomous agents operating across clouds. OAuth and SAML rely on centralized identity providers, which creates bottlenecks and single points of failure. When an agent fleet scales to hundreds of nodes, centralized IAM becomes a liability.
The Agentic AI IAM framework from the Cloud Security Alliance addresses this directly. It recommends Decentralized Identifiers (DIDs) and Verifiable Credentials (VCs) as the foundation for agent identity in distributed systems.
What are DIDs and VCs?
- Decentralized Identifiers (DIDs): Unique, cryptographically verifiable identifiers that agents control independently, without relying on a central registry.
- Verifiable Credentials (VCs): Signed attestations that prove an agent’s attributes, roles, or permissions, issued by a trusted authority and verifiable by any party.
Here is a direct comparison of IAM approaches for AI agents:
| Approach | Identity Control | Scalability | Failure Risk | Agent Suitability |
|---|---|---|---|---|
| OAuth 2.0 | Centralized | Moderate | High (single provider) | Low |
| SAML | Centralized | Low | High | Very Low |
| DIDs and VCs | Decentralized | High | Low | High |
| Zero Trust with DIDs | Decentralized | High | Very Low | Excellent |
Zero Trust principles are a natural fit here. Rather than granting blanket access based on network location, Zero Trust models require continuous, context-based verification for every agent interaction. No agent is trusted by default, even if it is running inside your own infrastructure.
Pro Tip: Scope each agent’s credentials to the minimum permissions it needs for its specific role. This limits blast radius if a credential is compromised.
For practical implementation, follow networking best practices that combine DID-based identity with Zero Trust enforcement at every communication layer. With secure frameworks in place, you can move to implementation specifics.
Step-by-step: Implementing blockchain-anchored agent communication
The BlockA2A framework provides a concrete architecture for securing agent-to-agent communication. It combines DIDs, smart contracts, and a Defense Orchestration Engine (DOE) to deliver sub-second attack response times. Here is how to implement it.
Step 1: Register agent DIDs Generate a DID for each agent at provisioning time. Anchor the DID document on your chosen blockchain or distributed ledger. This creates an immutable identity record that any party can verify without contacting a central server.
Step 2: Issue Verifiable Credentials Your trust authority issues VCs to each agent, encoding its role, permissions, and expiry. Agents present these credentials when initiating communication. Receiving agents verify the credential signature before accepting any request.
Step 3: Deploy smart contracts for access control Write smart contracts that encode your access policies. When an agent requests a resource or action, the contract evaluates the credential and either approves or denies the request on-chain. This removes the need for a centralized policy engine.
Step 4: Configure the Defense Orchestration Engine The DOE monitors agent interactions in real time. When it detects anomalous behavior, it triggers automated responses, isolating the affected agent and revoking its credentials within milliseconds.
Step 5: Test across your multi-cloud topology Use your multi-agent networking guide to validate connectivity and trust flows across all cloud providers before going to production.
Here are critical configuration benchmarks to target:
| Parameter | Recommended Value |
|---|---|
| Credential expiry | 1 to 4 hours |
| DOE response latency | Under 1 second |
| Smart contract audit cycle | Every 30 days |
| DID rotation frequency | Per session or daily |
Pro Tip: Use P2P networking for agents to eliminate centralized message brokers entirely. Direct peer connections reduce the number of intermediaries that can be compromised.
For multi-cloud setups, ensure your DID registry and smart contracts are accessible from all cloud environments without creating a new centralized dependency. After setting up your system, validating its security is crucial.
Verification and monitoring: Auditing agent security in production
Deployment is not the finish line. Continuous verification is what keeps your agent network secure as it scales and evolves. You need automated tools, clear metrics, and a testing strategy that matches the sophistication of modern attacks.
Automated benchmarks like ARTEMIS and ConVerse give you a structured way to measure your network’s resilience. Empirical data shows that human and AI testers uncover different vulnerability classes at different rates, which means relying on either alone leaves gaps. Layer both.
Essential logs and metrics to monitor in production:
- Credential presentation failures: Spikes indicate impersonation attempts or misconfigured agents.
- Unusual inter-agent request volumes: Sudden increases may signal a compromised agent probing the network.
- Smart contract revert rates: High revert rates on access control contracts point to policy mismatches or active attacks.
- DOE trigger frequency: Track how often automated defenses activate and investigate patterns.
- DID resolution latency: Degradation here can indicate infrastructure stress or targeted denial-of-service.
- Patch validation rates: Confirm that credential and contract updates propagate correctly across all nodes.
For real-world testing, run adversarial simulations against your agent network on a regular schedule. Use red team exercises that specifically target credential theft and lateral movement. Bug bounty programs focused on agent communication paths surface issues that automated tools miss.
Review your network infrastructure guide to align your monitoring setup with the specific protocols your agents use. Also verify that your secure communication protocols are correctly enforced at every layer, not just at the perimeter.
“Continuous improvement in agent security means treating every patch, credential rotation, and contract update as a testable event, not a routine maintenance task.”
Beyond technical how-tos, consider a strategic viewpoint for sustainable security.
Our take: Moving beyond legacy paradigms for AI network security
Here is what most security guides will not tell you: patching your existing IAM model to support agents is not a long-term strategy. It is a delay tactic. Centralized identity providers create chokepoints that scale poorly and fail catastrophically. As your autonomous agent networking grows, those chokepoints become your biggest liability.
Real resilience in multi-cloud agent environments comes from decentralizing trust entirely. When each agent holds its own cryptographic identity and credentials are verified peer-to-peer, there is no single point to compromise. The network degrades gracefully under attack rather than collapsing.
The teams that will stay ahead of emerging threats are the ones building self-sovereign identity and automated defense into their agent architecture from day one, not retrofitting it later. The threat frontier will keep moving. Your security model needs to move with it, not chase it.
Next steps: Secure your AI agent network with the right infrastructure
This guide gives you a clear path from threat awareness to production-grade security for your agent networks. The frameworks, steps, and monitoring practices here are grounded in current research and real deployment patterns.

If you want to go deeper on the infrastructure side, the Pilot Protocol research on agent communication infrastructure is a strong next read. It covers the foundational networking problems that decentralized agent systems face and how purpose-built infrastructure addresses them. When you are ready to build or upgrade your agent network, Pilot Protocol provides the encrypted P2P connectivity, virtual addressing, and NAT traversal your agents need to communicate securely across any cloud.
Frequently asked questions
What is the primary security risk for AI agents in decentralized networks?
Credential compromise and impersonation remain the top risks, as attackers who steal agent tokens can gain unauthorized access or silently disrupt agent coordination across the entire network.
How do Decentralized Identifiers (DIDs) improve security for agent communication?
DIDs give agents unique, cryptographically verifiable identities that no central provider controls, which eliminates the wide-scale impersonation risk that comes with shared identity registries.
Why is Zero Trust especially important for agent networks?
Zero Trust enforces continuous verification at every interaction, which prevents a single compromised agent from moving laterally through a distributed environment unchecked.
What is the Defense Orchestration Engine (DOE) in BlockA2A?
The DOE detects and neutralizes attacks in real time with sub-second latency, using blockchain-anchored trust records to validate agent identity and revoke credentials instantly when anomalies are detected.
How effective are AI agents at finding security vulnerabilities compared to humans?
ARTEMIS benchmark results show that AI agents can outperform most human testers at vulnerability discovery, achieving over 80% precision on valid findings in structured evaluations.


