Secure AI agent networking workflow: step-by-step guide
Secure AI agent networking workflow: step-by-step guide
TL;DR:
- Proper configuration is essential to prevent exposure to unauthorized access, data leaks, and failures.
- Hybrid networking models combining centralized policy enforcement and decentralized P2P transport offer optimal security.
- Implementing end-to-end encryption, strong authentication, NAT traversal, and continuous monitoring ensures resilient AI agent networks.
Misconfigured agent networking is one of the fastest ways to expose your infrastructure to unauthorized access, data leaks, and cascading failures across cloud regions. As autonomous AI agents take on more critical tasks, the networking layer connecting them becomes a serious attack surface. Centralized brokers introduce single points of failure, while naive P2P setups leave agents vulnerable behind NAT and firewalls. This guide walks you through the exact steps to design and deploy a secure, resilient networking workflow for AI agents in multi-cloud environments, drawing on research-backed approaches like SAGA and AgentAnycast.
Table of Contents
- Understanding secure networking requirements for AI agents
- Preparing your environment: Key components and prerequisites
- Step-by-step: Building a secure agent networking workflow
- Verifying security and troubleshooting common networking pitfalls
- Why hybrid networking models are the future of secure AI agents
- Take your AI agent networking further
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Requirements first | Define strict networking and security requirements before selecting protocols or tooling. |
| Combine approaches | Blending centralized and decentralized models helps solve resilience and security gaps in agent workflows. |
| End-to-end encryption | Use end-to-end encrypted communication channels by default to shield agent traffic from interception. |
| Continuous verification | Routinely audit your workflows for protocol or configuration weaknesses before and after deployment. |
Understanding secure networking requirements for AI agents
To address these challenges, start by clarifying your networking and security criteria. Building AI agent network infrastructure without a clear requirements map leads to gaps that attackers exploit. The core requirements for any secure agent networking workflow include:
- Strong authentication: Every agent must prove its identity before joining a network or exchanging data.
- Encrypted communication: All traffic between agents must be encrypted in transit, with no plaintext fallback.
- NAT and firewall traversal: Agents deployed behind corporate firewalls or in private subnets must still reach peers reliably.
- Interoperability: Agents using different protocols (A2A, ACP, CORAL) must communicate without security degradation.
- Policy enforcement: Access rules must be applied consistently, regardless of where agents run.
Two leading architectural models address these requirements differently. SAGA provides centralized policy enforcement and secure inter-agent TLS communication, making it well suited for environments where compliance and auditability are priorities. AgentAnycast enables decentralized P2P networking for agents behind NAT and firewalls, removing the need for a central broker entirely. Understanding the tradeoffs between these models is essential before you write a single line of configuration.
| Requirement | SAGA (centralized) | AgentAnycast (decentralized) | Relevant protocol |
|---|---|---|---|
| Authentication | Centralized identity provider | DID-based identity | TLS, OAuth2 |
| Encrypted transport | TLS between agents | Noise_XX E2E encryption | TLS, Noise Protocol |
| NAT traversal | Requires public endpoints | Built-in NAT punch-through | STUN, TURN |
| Policy enforcement | Central policy engine | Distributed access tokens | RBAC, ACLs |
| Fault tolerance | Single point of failure risk | Resilient by design | N/A |
“Relying on a single centralized control plane for agent communication creates a systemic risk. If that plane fails or is compromised, every agent in your fleet loses its ability to operate securely.”
The NIST AI agent standards initiative launched in 2026 is actively developing interoperability and security standards for agent networks. Tracking this work now will save you significant rework later. Review the AI networking protocol explanations to align your vocabulary and design choices with emerging standards before you finalize your architecture.
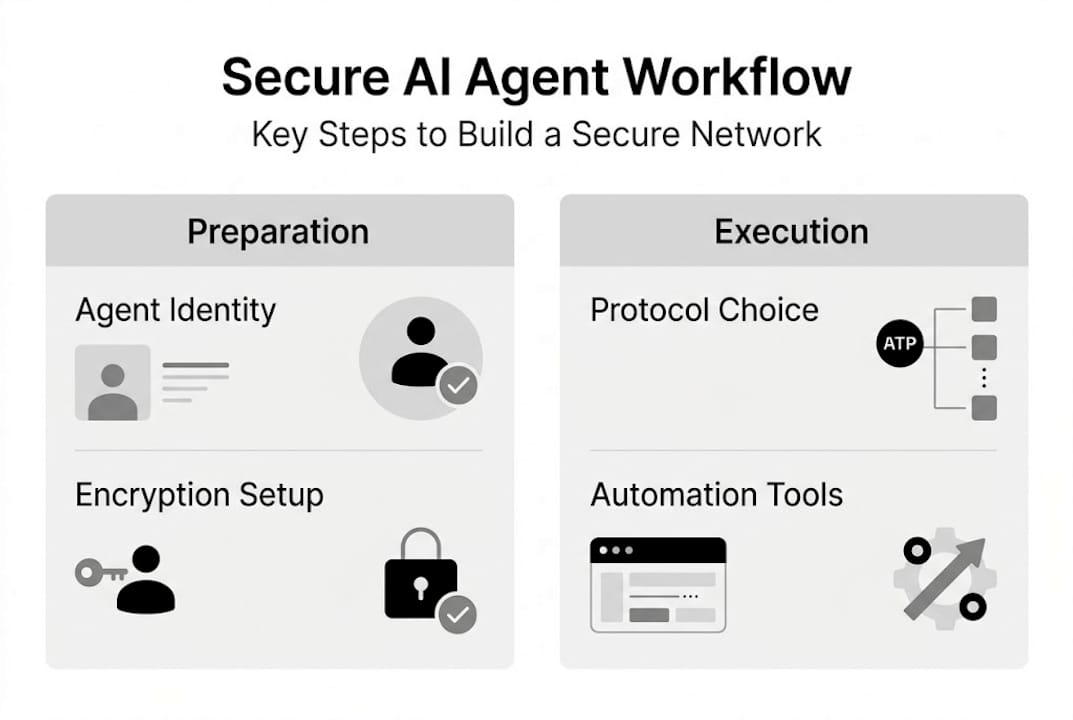
Preparing your environment: Key components and prerequisites
Once the networking requirements are understood, gather and configure the necessary infrastructure. Skipping this step leads to integration failures mid-deployment, which are expensive to fix under production pressure.
Here is what you need to prepare:
- Multi-cloud access credentials: Ensure your agents can authenticate with each cloud provider’s API without hardcoded secrets.
- Cryptographic key management: Use a secrets manager (AWS Secrets Manager, HashiCorp Vault, or equivalent) to store and rotate agent keys.
- Agent identity system: Assign each agent a persistent, verifiable identity. Decentralized identifiers (DIDs) are the recommended standard for P2P environments.
- Secure protocol support: Confirm your runtime supports TLS 1.3 or the Noise Protocol Framework.
- Monitoring and logging: Set up centralized log aggregation before agents go live, not after an incident.
AgentAnycast supports DID identity and Noise Protocol-based end-to-end encryption, making it a strong fit for P2P solutions for agent networking where you cannot guarantee public IP availability. DIDs give each agent a cryptographically verifiable identity that does not depend on a central authority, which is foundational for cross-cloud interoperability.
| Component | Role | Recommended tool |
|---|---|---|
| Agent identity | Unique, verifiable agent ID | DID, X.509 certificates |
| Transport security | Encrypt all agent traffic | TLS 1.3, Noise_XX |
| Policy enforcement | Control who can talk to whom | OPA, RBAC policies |
| Key management | Secure credential storage and rotation | Vault, AWS Secrets Manager |
| Monitoring | Detect anomalies and audit access | Prometheus, ELK Stack |
| Fallback strategy | Handle connectivity failures gracefully | Circuit breakers, retry logic |
End-to-end encryption is non-negotiable. The benefits of encrypted tunnels in P2P agent networks go beyond confidentiality. Encrypted tunnels also prevent traffic analysis attacks, where an adversary infers agent behavior from packet timing and size without ever decrypting the payload.
Pro Tip: Use a sidecar architecture, similar to how AgentAnycast is deployed, to handle all networking and encryption logic separately from your core agent code. This keeps your agent logic clean and lets you swap networking layers without rewriting business logic.
Step-by-step: Building a secure agent networking workflow
With all components in place, you can now execute the secure workflow step by step.
- Register each agent with a persistent identity. Assign a DID or certificate to every agent at provisioning time. Store credentials in your secrets manager, never in environment variables or container images.
- Authenticate agents before any data exchange. Use mutual TLS (mTLS) for centralized deployments or DID-based handshakes for P2P setups. No agent should receive data from an unauthenticated peer.
- Establish encrypted channels. For centralized architectures, configure TLS between agents and the policy engine. For decentralized setups, use Noise_XX for direct agent-to-agent encryption. Learn more about secure tunnel setup for agents to choose the right approach.
- Enforce access control policies. SAGA enforces policy using cryptographically signed access control tokens, ensuring that only authorized agents can invoke specific capabilities. Replicate this pattern in your own setup using signed JWTs or OPA policies.
- Enable NAT traversal for cross-cloud agents. AgentAnycast supports E2E encrypted communication and NAT traversal, so agents behind private subnets can still reach peers directly without opening inbound firewall rules.
- Implement continuous monitoring. Log every authentication event, policy decision, and channel establishment. Alert on anomalies in real time.
| Step | SAGA (centralized) | AgentAnycast (decentralized) |
|---|---|---|
| Identity registration | Central identity provider | DID registry |
| Authentication | mTLS with central CA | DID-based handshake |
| Encrypted transport | TLS to policy engine | Noise_XX direct P2P |
| Policy enforcement | Signed access tokens | Distributed ACLs |
| NAT traversal | Requires public endpoints | Built-in punch-through |
| Scale-out | Horizontal broker scaling | Peer discovery, no broker |
Protocol choice matters at step 3. Review your secure protocol options to understand where A2A, ACP, and CORAL each fit, and where they introduce risk.
Pro Tip: Use Terraform or Ansible to automate agent registration and channel configuration across cloud providers. Manual configuration at scale is the leading cause of security drift in multi-cloud agent deployments.
Verifying security and troubleshooting common networking pitfalls
After implementation, robust verification and troubleshooting are crucial to maintaining security. A deployment that looks correct can still harbor misconfiguration that only surfaces under specific network conditions.
Security verification checklist:
- Confirm all agent channels use TLS 1.3 or Noise_XX. Reject any connection using older cipher suites.
- Verify credential rotation is automated and that no agent holds a key older than your defined rotation period.
- Test policy enforcement by attempting unauthorized agent-to-agent calls. These must be rejected with a logged denial.
- Audit DID or certificate revocation lists to ensure compromised agent identities are invalidated immediately.
- Run NAT traversal tests from private subnets in each cloud region to confirm connectivity without public IP exposure.
Common troubleshooting scenarios:
- NAT traversal failures: Check that your STUN/TURN configuration is correct and that UDP is not blocked at the subnet level. AgentAnycast’s built-in punch-through handles most cases, but restrictive corporate firewalls may require TCP fallback.
- Protocol mismatches: Agents using different protocol versions will fail to establish channels silently. Enforce version pinning in your deployment manifests.
- Identity revocation delays: If a compromised agent continues to communicate after revocation, your revocation list propagation is too slow. Reduce the cache TTL on your identity validation layer.
“No single protocol provides complete security across all deployment scenarios. Hybrid approaches that combine strong authentication with encrypted transport and distributed policy enforcement offer the most resilient posture.”
Comparative security analysis shows that protocol flaws and real-world implementation gaps make hybrid approaches essential for resilience and confidentiality. A 14-point vulnerability taxonomy across agent communication protocols reveals that even architecturally sound protocols suffer from implementation-level weaknesses. Apply zero trust for agent comms principles to limit blast radius when a single agent or protocol layer is compromised. Review AI networking challenges for a broader look at where decentralized systems commonly break down.
Why hybrid networking models are the future of secure AI agents
Looking forward, it is worth reconsidering the traditional tradeoff between centralized and decentralized designs. Most teams default to one model based on familiarity, not fitness. That is a mistake.
No universal protocol fits all scenarios. Dynamic hybrid approaches that balance resilience and confidentiality outperform pure centralized or decentralized protocols across real-world threat models. The teams seeing the best results are those actively blending SAGA-style policy enforcement with AgentAnycast-style P2P transport, selecting the right layer for each security objective. A ProtocolRouter that selects communication paths based on current threat context, latency requirements, and compliance constraints is not a future concept. It is something you can build today with the tools covered in this guide.
We also recommend tracking the NIST initiative closely. Standards shape tooling, and tooling shapes what is practical to deploy at scale. Explore decentralized protocol strategies to stay ahead of the curve as these standards mature.
Pro Tip: Revisit your protocol selection quarterly. The threat landscape for AI agent networks is evolving faster than most teams update their architecture documentation.
Take your AI agent networking further
If you are ready to go deeper or streamline your next deployment, specialized resources can help you move faster without sacrificing security.

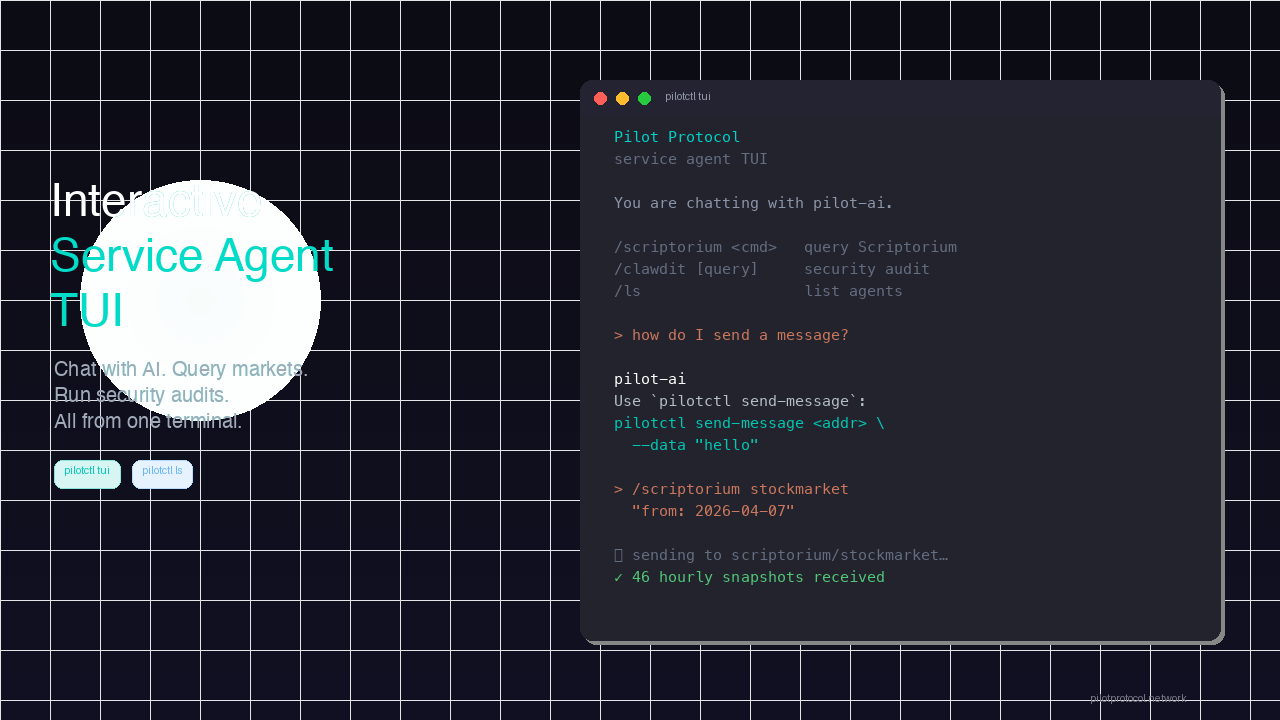
The Pilot Protocol platform provides decentralized networking infrastructure built specifically for AI agents, with built-in NAT traversal, encrypted tunnels, persistent virtual addresses, and trust establishment across multi-cloud environments. You do not need to stitch together separate tools for each layer. Explore the secure infra guide for hands-on implementation details, advanced configuration patterns, and architecture templates you can adapt directly to your fleet. Start building secure, scalable agent networks today.
Frequently asked questions
What is the biggest security risk for autonomous AI agent networking?
The biggest risks include unsecured credentials, protocol flaws, and misconfigured firewalls, which can expose your agents to unauthorized access or data breaches. Even architecturally sound protocols like CORAL suffer from real-world implementation weaknesses that attackers can exploit.
Do I need public IPs to enable P2P agent networking?
No. AgentAnycast enables P2P networking with built-in NAT traversal and end-to-end encryption, so your agents can connect directly even when public IP addresses are unavailable.
Are centralized or decentralized workflows more secure for multi-cloud agent deployments?
Neither model wins outright. Hybrid models optimize resilience and confidentiality better than pure centralized or decentralized protocols, making a blended approach the most practical choice for production multi-cloud deployments.
What standards exist for secure AI agent networking workflows?
NIST launched an initiative in 2026 focused on interoperable, secure AI agent standards, covering identity, access control, and communication frameworks that will shape tooling across the industry.