AI networking terminology explained: A2A, MCP, ANP protocols
AI networking terminology explained: A2A, MCP, ANP protocols
AI agents don’t just “talk” to each other the way humans message on a phone. The reality is far more structured, and far more consequential for your infrastructure. AI networking terminology covers a rapidly evolving set of protocols, including A2A (Agent-to-Agent), MCP (Model Context Protocol), and ANP (Agent Network Protocol), each targeting different layers of agent communication. If you’re building autonomous agent fleets or cross-cloud orchestration pipelines, getting these distinctions right isn’t optional. It directly affects your security posture, scalability, and how much technical debt you accumulate before your first production incident.
Table of Contents
- Decoding AI networking terminology: The landscape clarified
- A2A, MCP, and ANP protocols: How do they work in practice?
- Security and trust models: Navigating authentication and privacy
- Benchmarks and real-world challenges: What works and what breaks?
- The future of AI networking: Why a hybrid protocol approach leads
- Level up your AI networking: Reliable protocols for next-gen agents
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Protocol diversity matters | A2A, MCP, and ANP each serve distinct use cases for agent-to-agent, agent-to-tool, and decentralized communication. |
| Security is protocol-dependent | Authentication and privacy mechanisms differ dramatically across protocols, impacting deployment risk and compliance. |
| Benchmarks expose limitations | Current benchmarks show decentralized protocols lag in maturity and performance, making hybrid approaches more reliable in 2026. |
| Hybrid strategy recommended | Combining mature centralized (A2A) and tool-centric (MCP) protocols is the pragmatic choice for scalable AI networking today. |
Decoding AI networking terminology: The landscape clarified
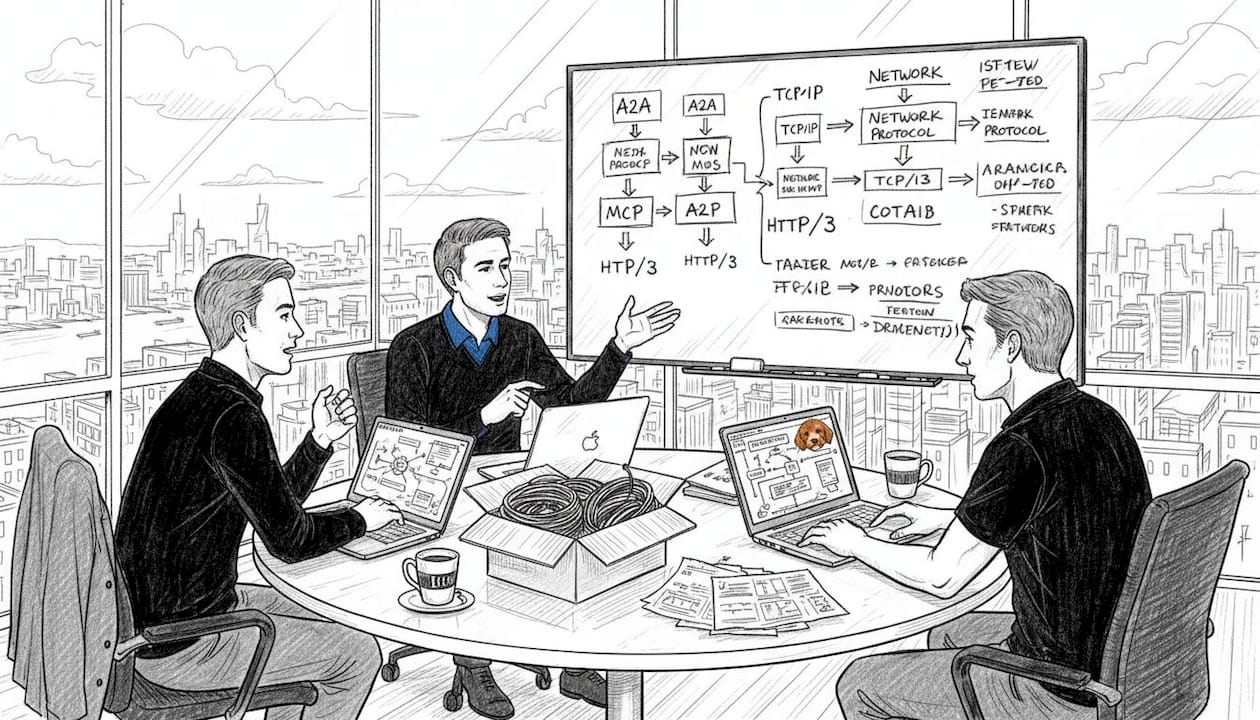
The first thing to understand is that A2A, MCP, and ANP are not competing alternatives to the same problem. They solve different problems at different layers. Treating them as interchangeable is a common mistake that leads to mismatched architectures.
Here’s a quick breakdown of each:
- A2A (Agent-to-Agent): Designed for direct collaboration between autonomous agents. Handles discovery, task delegation, and streaming results between agents in an enterprise setting.
- MCP (Model Context Protocol): Focuses on agent-to-tool connections. Standardizes how agents access external tools, APIs, and data sources using prompt-based orchestration.
- ANP (Agent Network Protocol): A decentralized mesh approach. Uses decentralized identifiers (DIDs) for trustless, federated agent communication across organizational boundaries.
The centralized and decentralized protocols distinction matters here. Centralized vs. decentralized design reflects real trade-offs in trust, infrastructure requirements, and protocol maturity. A2A assumes a managed environment with identity infrastructure. ANP, as documented in the ANP documentation, assumes no central authority and relies on cryptographic identity.
| Protocol | Primary role | Trust model | Maturity |
|---|---|---|---|
| A2A | Agent-to-agent collaboration | Centralized (OAuth) | Production-ready |
| MCP | Agent-to-tool integration | Semi-centralized | Widely adopted |
| ANP | Decentralized agent mesh | Trustless (DIDs) | Experimental |
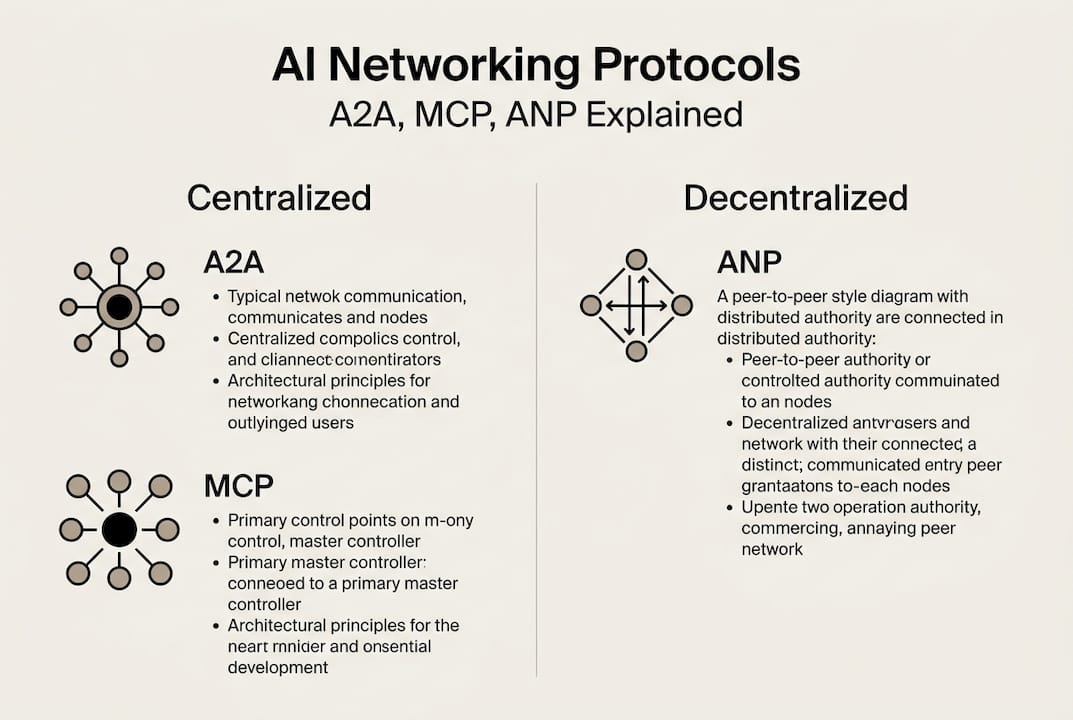
Knowing which layer you’re operating on determines which protocol belongs in your stack. Most production systems in 2026 use A2A and MCP together, with ANP reserved for federated or privacy-sensitive use cases.
A2A, MCP, and ANP protocols: How do they work in practice?
With the terminology mapped out, let’s look at how each protocol actually operates in a real deployment.
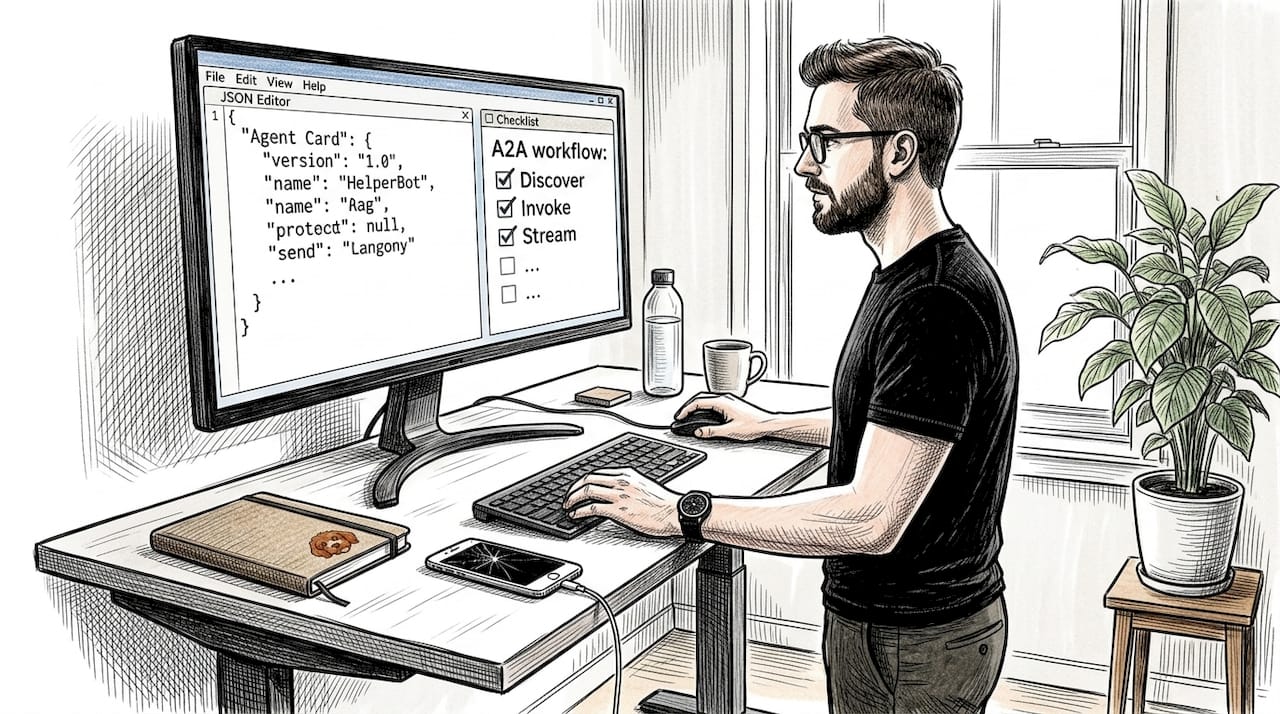
A2A in practice
A2A uses OAuth, Agent Cards, and a structured task lifecycle: discover, invoke, stream results. An Agent Card is a signed JSON document that describes an agent’s capabilities, endpoints, and authentication requirements. When Agent A needs to delegate a task to Agent B, it fetches Agent B’s card, authenticates via OAuth, and initiates a task session. Results can stream back in real time.
MCP in practice
MCP uses JSON-RPC over HTTP/SSE and eliminates the N×M integration problem, where every agent needs a custom connector for every tool. Instead, tools expose a standard MCP interface, and any compliant agent can use them. See the MCP standard details for the full spec. You can also explore how MCP in enterprise systems and connecting MCP servers work in practice.
ANP in practice
ANP provides a trustless stack using DIDs and a meta-protocol negotiation layer. Agents first establish identity via a DID document, then negotiate which sub-protocols to use for the actual data exchange. This makes ANP highly flexible but also more complex to deploy.
Here’s a simplified workflow comparison:
- A2A: Fetch Agent Card → OAuth handshake → Send task → Receive streamed results
- MCP: Connect to MCP server → List available tools → Call tool via JSON-RPC → Process response
- ANP: Resolve DID → Meta-protocol negotiation → Establish encrypted channel → Exchange semantic data
| Protocol | Transport | Auth method | Streaming support |
|---|---|---|---|
| A2A | HTTP/JSON-RPC | OAuth 2.0 | Yes |
| MCP | HTTP/SSE | API key or OAuth | Yes |
| ANP | Flexible | DID-based | Negotiated |
Pro Tip: If you’re starting a new agent project in 2026, implement MCP for tool access first. It’s the fastest path to a working integration layer, and you can layer A2A on top for agent-to-agent delegation once your tool ecosystem is stable.
Security and trust models: Navigating authentication and privacy
Practical operation often reveals the hidden intricacies of security and privacy. Let’s examine the trust models that underpin these protocols.
A2A leverages OAuth and signed Agent Cards, while ANP relies on end-to-end encryption via DIDs. These aren’t just implementation details. They represent fundamentally different threat models.
A2A security profile:
- OAuth 2.0 for agent authentication
- Signed Agent Cards to verify capability claims
- Centralized identity provider required
- Vulnerable to compromised OAuth tokens
ANP security profile:
- DID-based identity, no central authority
- End-to-end encryption by default
- Decentralized systems avoid intermediaries but require DID infrastructure to be in place
- Negotiation overhead can introduce latency and attack surface
MCP security profile:
- Prompt injection is the primary risk vector
- Tool responses can contain adversarial content that manipulates agent behavior
- Requires careful input validation at every tool boundary
For teams building cross-organizational agent networks, the zero trust AI networking model is the right frame. Every agent interaction should be authenticated and authorized, regardless of network position. The AI agent network stacks post covers this in more depth.
Key insight: The IETF’s current analysis of AI networking challenges confirms that no single protocol fully addresses all security requirements. Defense-in-depth remains essential.
Pro Tip: For MCP deployments, treat every tool response as untrusted input. Implement a validation layer between the MCP server response and your agent’s reasoning loop to block prompt injection attempts before they reach the model.
Benchmarks and real-world challenges: What works and what breaks?
Understanding terminology and principles is one thing. Examining real-world data reveals how protocols perform under pressure.
The COMMA benchmark results are sobering. SOTA models like GPT-4o fail agent-to-agent collaboration tasks at rates that would be unacceptable in production, and no public benchmarks currently exist for ANP or similar decentralized protocols. You’re essentially flying blind if you deploy ANP at scale today.
The benchmark data also shows an important architectural insight: Anemoi, a semi-centralized system, outperforms OWL, a decentralized alternative, on GAIA benchmarks in practical scenarios. This isn’t a minor gap. It reflects a structural advantage that centralized coordination provides in complex multi-step tasks.
Key challenges by protocol:
- A2A: Assumes agent catalogs exist and are maintained. In dynamic environments, catalog staleness causes discovery failures.
- MCP: Scales well for tool access but doesn’t handle agent-to-agent state management natively.
- ANP: Negotiation overhead is high. In latency-sensitive pipelines, this becomes a bottleneck. No protocol benchmark comparisons exist for ANP in production-scale deployments.
The multi-agent networking failures you’re most likely to encounter in 2026 are not protocol bugs. They’re architectural mismatches: using ANP where A2A fits better, or expecting MCP to handle agent coordination it was never designed for. The AI networking challenges in decentralized systems go deeper than most teams anticipate before their first real deployment.
Statistic to keep in mind: Current COMMA results show that even top-tier models fail collaborative agent tasks at rates that make purely autonomous multi-agent pipelines unreliable without human-in-the-loop checkpoints.
The future of AI networking: Why a hybrid protocol approach leads
Here’s the candid take that benchmark data and field experience support: the hype around fully decentralized AI agent communication is ahead of the reality.
ANP is genuinely interesting. The vision of trustless, federated agent networks operating across organizational boundaries without central brokers is compelling. But prioritizing robust A2A/MCP hybrid patterns for reliability is the right call for 2026 production deployments, because decentralized protocols remain unproven at scale.
The teams we see succeeding are the ones who resist the urge to build on the most architecturally elegant solution and instead build on the most operationally proven one. A2A handles agent-to-agent delegation. MCP handles tool access. Together, they cover 90% of what most agent systems actually need. You can find deeper analysis of this in our AI networking strategy insights.
Watch ANP, HMP, and Coral closely. Contribute to their development if you have the capacity. But treat them as R&D investments, not production dependencies. The benchmark gaps are real, the infrastructure requirements are significant, and the operational tooling isn’t there yet. Build for what works now, and architect your system so you can swap in decentralized components as they mature.
Level up your AI networking: Reliable protocols for next-gen agents
You now have a clear map of A2A, MCP, and ANP, how they work, where they break, and how to combine them effectively. The next step is putting that knowledge into a real infrastructure layer that your agents can rely on.

The Pilot Protocol platform gives your engineering team the tools to build exactly that. Pilot Protocol provides encrypted peer-to-peer tunnels, NAT traversal, virtual addressing, and trust establishment for AI agent fleets, without requiring centralized message brokers. Whether you’re connecting MCP servers across regions, securing A2A task delegation, or preparing your architecture for decentralized protocols, Pilot Protocol handles the networking layer so your agents can focus on the work. Explore the CLI and SDKs to get your first agent network running today.
Frequently asked questions
What does A2A mean in AI networking?
A2A stands for Agent-to-Agent, a protocol enabling direct collaboration between autonomous AI agents with features like agent discovery, OAuth authentication, and task streaming. It’s currently the most mature enterprise option for agent-to-agent delegation.
How is MCP different from A2A and ANP?
MCP standardizes agent-to-tool connections using JSON-RPC and prompt-based resource access, not direct agent-to-agent communication. Think of it as the integration layer between your agents and the external tools they use.
What security risks should I know about with these protocols?
The main risks are MCP prompt injection, ANP negotiation overhead, and catalog staleness in A2A, all of which require explicit threat modeling and mitigation strategies in your architecture.
Why aren’t decentralized protocols like ANP widely used yet?
ANP remains experimental compared to A2A’s production maturity, with significant challenges in negotiation overhead, DID infrastructure requirements, and a complete absence of public performance benchmarks.
Are there benchmarks for agent networking performance?
COMMA benchmarks reveal gaps in real-world multi-agent performance, and no public benchmark data currently exists for fully decentralized protocols like ANP or Coral, making production risk assessment difficult.


