Protocol wrapping for secure peer-to-peer AI systems
Protocol wrapping for secure peer-to-peer AI systems
TL;DR:
- Most overlay networks rely on protocol wrapping to navigate complex network environments rather than inventing new protocols.
- Encapsulation allows secure, flexible peer-to-peer communication across NATs, firewalls, and cloud boundaries.
- Extensible protocols like Geneve support future metadata needs and enhanced privacy for AI and decentralized systems.
Most engineers assume that building a new overlay network means inventing new protocols from scratch. The reality is almost the opposite. The vast majority of modern P2P and overlay networks work by wrapping existing protocols inside other protocols to traverse hostile, unsupportive network environments. Protocol wrapping is fundamental in modern overlay networks for secure peer-to-peer communication, yet many distributed systems engineers treat it as a legacy or niche concept. This guide breaks down the mechanics, real-world use cases, performance benchmarks, and advanced privacy strategies you need to build secure, scalable AI agent networks.
Table of Contents
- Understanding protocol wrapping: Definition and context
- The mechanics: How protocol wrapping works
- Use cases and real-world benchmarks
- Privacy, security, and extensibility: Advanced wrapping strategies
- A practitioner’s take: What most engineers miss about protocol wrapping
- Take the next step with cutting-edge overlay networking
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Universal tool | Protocol wrapping is essential for building secure and flexible decentralized networks. |
| Performance advantages | UDP overlay wrappers offer faster connections and less memory usage for P2P communication than traditional HTTP transports. |
| Future-proof designs | Extensible protocols like Geneve and metadata-aware wrappers support rapid innovation and privacy in distributed AI systems. |
| Benchmark-driven choices | Real-world benchmarks reveal that protocol selection impacts not just speed but privacy and operational scaling for agent networks. |
Understanding protocol wrapping: Definition and context
At its core, protocol wrapping is encapsulation. You take a payload that a network cannot natively route or support, enclose it inside a protocol frame that the network does understand, and send it through. The receiving end strips the outer frame and reads the original payload. Protocol wrapping enables sending unsupported payloads through network layers by enclosing data in other protocol frames.
Think of it this way: you have a package that a courier will not accept because of its shape. You put it in a standard box the courier recognizes, ship it, and the recipient opens the box to find the original package inside. That is exactly what protocol wrapping does at the network layer.
This approach is foundational across a wide range of systems. Overlay networks use it to create virtual topologies on top of physical infrastructure. VPNs use it to tunnel private traffic over public internet. AI agent swarms use it to communicate directly across cloud boundaries and NAT barriers. Decentralized systems use it to maintain persistent, encrypted channels without relying on central brokers.
Here are the top three reasons protocol wrapping is essential for AI and decentralized networking:
- NAT traversal: Most agents run behind NAT devices that block unsolicited inbound connections. Wrapping protocols inside UDP allows hole-punching and relay fallback to succeed where raw TCP would fail.
- Protocol flexibility: You can run gRPC, HTTP, or SSH inside an encrypted overlay without changing the application layer. This makes wrapping critical for integrating legacy systems into modern agent fleets.
- Security layering: Wrapping adds an encryption and authentication boundary at the transport level, independent of what the inner protocol supports.
You can explore protocol overlay fundamentals to understand how these layers interact in practice, and see how serverless agent communication builds directly on these concepts.
“Encapsulation is not a workaround. It is the standard mechanism by which modern distributed systems achieve interoperability across heterogeneous network environments.”
Now that you know why protocol wrapping matters, let’s break down its mechanics and real-world applications.
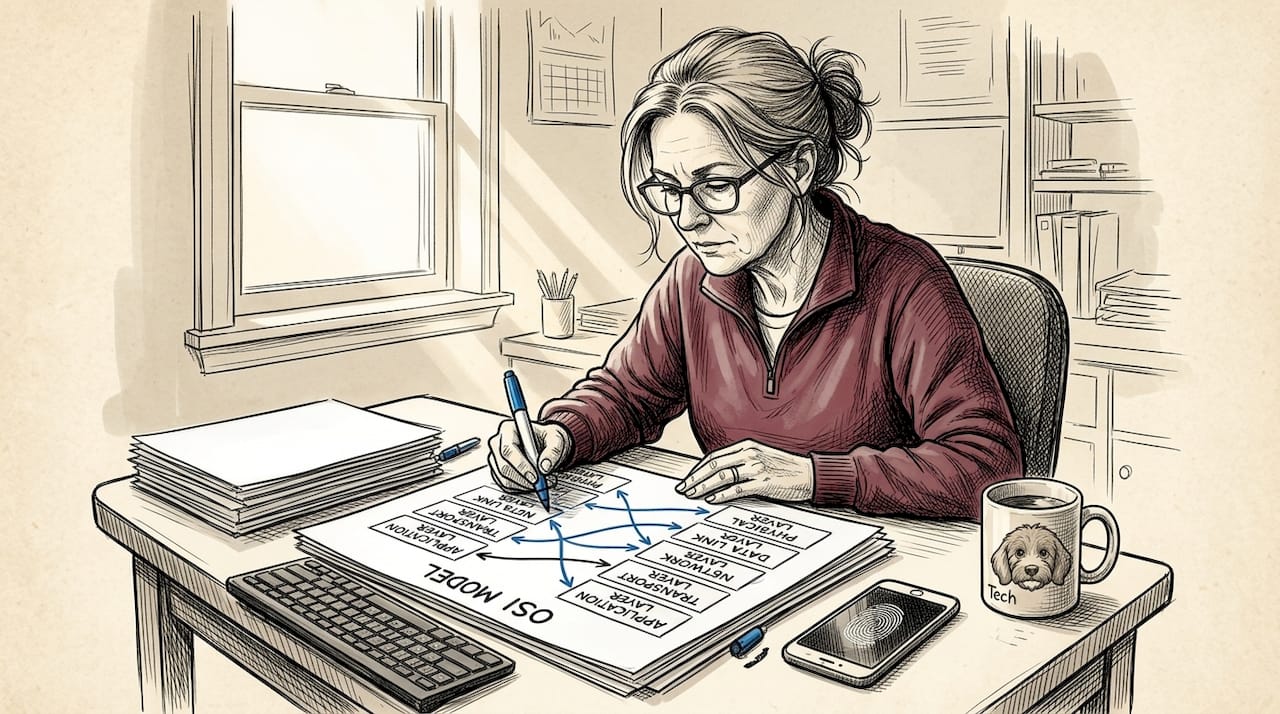
The mechanics: How protocol wrapping works
With the fundamentals in mind, it’s time to examine how wrapping functions in practice. The process follows three clear steps:
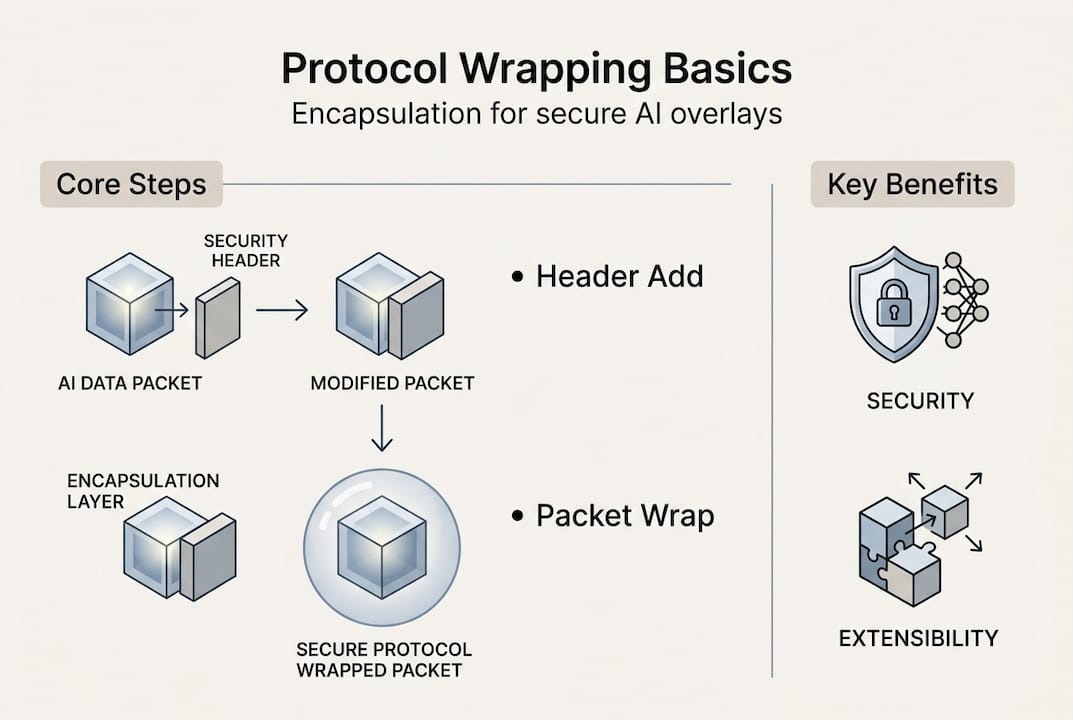
- Encapsulate: The sender takes the original packet (the inner payload) and prepends a new header from the outer protocol. For VXLAN, this means adding a UDP header, an IP header, and a VXLAN header containing a 24-bit Virtual Network Identifier (VNI). For Geneve, the outer header includes Type-Length-Value (TLV) fields that carry extensible metadata.
- Transmit: The wrapped packet travels through the network as a standard UDP/IP datagram. Intermediate routers and firewalls see only the outer header and route accordingly. They have no visibility into the inner payload.
- Decapsulate: The receiving endpoint identifies the outer protocol, strips the encapsulation headers, and delivers the original packet to the appropriate virtual network or application.
Mechanics involve header addition and UDP/IP wrapping for L3 traversal, with VXLAN and Geneve being the most widely deployed examples.
Here is a direct comparison of the three major encapsulation protocols you will encounter:
| Protocol | Outer header | Key feature | Extensibility | Segment limit |
|---|---|---|---|---|
| VXLAN | UDP + IP | 24-bit VNI | Fixed | 16 million segments |
| Geneve | UDP + IP | TLV metadata fields | High | 16 million segments |
| MPLSoUDP | UDP + IP | Label stacking | Moderate | Label-based |
VXLAN is the most widely deployed, but its fixed header limits adaptability. Geneve’s TLV support lets you carry arbitrary metadata alongside the payload, which is critical when your AI agents need to pass trust tokens, routing hints, or telemetry data inside the tunnel itself. MPLSoUDP is common in carrier-grade environments where label-switched paths are already in use.
Pro Tip: Prefer Geneve or another extensible encapsulation standard when building new agent overlays. VXLAN is mature and stable, but its fixed format will constrain you when regulatory requirements or new security standards demand metadata changes. See how Pilot Protocol works for a concrete example of extensible overlay design, and review multi-cloud agent connection strategies that rely on these mechanics.
Use cases and real-world benchmarks
Understanding the mechanics is crucial, but applying wrapping in the real world means knowing the scenarios and practical outcomes. Here are the most important use cases for protocol wrapping in AI and distributed systems:
- Virtual overlay networks: Create isolated, multi-tenant agent networks on shared cloud infrastructure without modifying the underlying hardware.
- VPN alternatives: Provide encrypted, direct agent-to-agent tunnels without the overhead and single points of failure that traditional VPN concentrators introduce.
- AI swarm networking: Allow large fleets of autonomous agents to discover, authenticate, and communicate with each other across cloud regions and NAT boundaries.
- Messaging privacy: Wrap application-layer messages inside encrypted transport to prevent traffic analysis and metadata leakage at the network level.
- P2P file transfer: Enable direct, high-throughput data exchange between agents without routing through central servers. See P2P file transfer strategies for implementation patterns.
The performance differences between wrapping strategies are significant. UDP overlays are 11x faster for connections and use far less RAM than HTTP/2 for agent P2P, but NAT relays reduce throughput when direct paths fail.
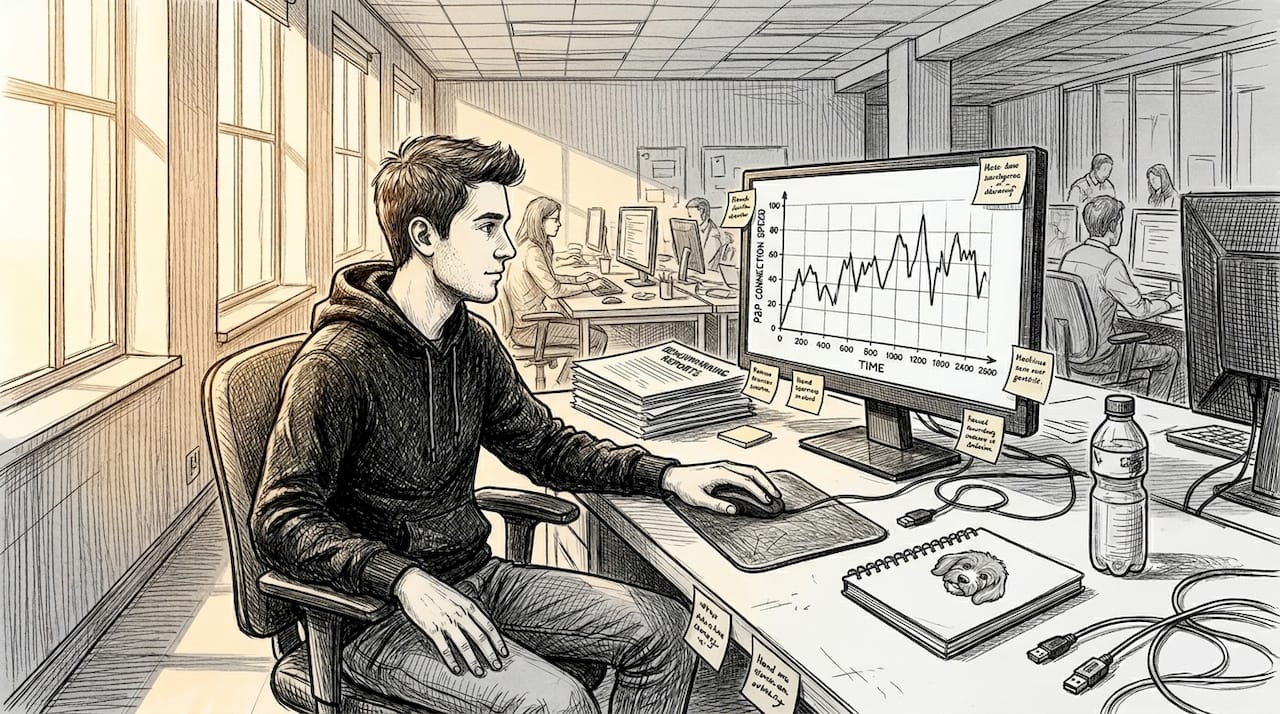
That 11x connection speed advantage is not marginal. For agent fleets that need to establish hundreds or thousands of connections per second, the difference between UDP overlay and HTTP/2 determines whether your system scales or stalls. Memory profile matters just as much. HTTP/2 connection state is expensive at scale. UDP overlays keep per-connection overhead low, which is critical when you are running thousands of agents on a single host.
The relay fallback issue deserves attention. In real deployments, roughly 10 to 15 percent of direct P2P connections fail due to symmetric NAT or firewall policies. When that happens, traffic routes through a relay node, and throughput drops. Your protocol choice, relay capacity, and fallback strategy need to account for this from the start. Research into anonymity wrappers shows that transport-layer wrapping decisions also affect privacy guarantees, not just speed.
Privacy, security, and extensibility: Advanced wrapping strategies
The real power of protocol wrapping appears when privacy, security, and future-proofing are top priorities. Metadata exposure is the most underestimated risk in overlay networking. Even when payload content is encrypted, the timing, size, and frequency of packets can reveal agent behavior, communication patterns, and network topology to an observer.
Two approaches address this directly: Anonymity Wrappers (AW) and Sealed Sender. Here is how they compare:
| Feature | Anonymity wrappers (AW) | Sealed Sender |
|---|---|---|
| Message size | Smaller | Larger |
| Anonymity strength | Strong | Moderate |
| Group message support | Yes | Limited |
| State exposure protection | Full forward secrecy | Partial |
| Post-compromise recovery | Yes | No |
Anonymity wrappers outperform Sealed Sender for message size and state privacy, and AWs provide forward secrecy even after compromise.
This matters for AI systems that handle sensitive data or operate in regulated environments. If an agent’s keys are compromised, AW-based designs ensure that past communications remain protected. Sealed Sender, while useful, does not provide the same guarantee.
For transport security, layering TLS or QUIC inside your overlay adds a second encryption boundary. This is valuable when you cannot fully trust the overlay infrastructure itself. Libp2p takes this further by combining protocol negotiation, encryption, and multiplexing into a single stack designed for decentralized systems.
Pro Tip: Build on Geneve or TLV-based encapsulation from the start. When post-quantum cryptography standards finalize, cross-cloud compliance requirements shift, or new metadata privacy regulations arrive, extensible protocols let you adapt without redesigning your entire overlay. See HTTP services over encrypted overlay for practical implementation, and review the Pilot Protocol overlay network specification for a reference architecture.
A practitioner’s take: What most engineers miss about protocol wrapping
Having covered the advanced mechanics, here is a ground-level perspective from practitioners who have deployed these systems at scale.
The biggest misconception is that protocol wrapping is primarily a technical decision. It is not. Network realities drive most design choices. You do not pick VXLAN because it is theoretically optimal. You pick it because your cloud provider supports it, your team knows it, and your timeline does not allow for Geneve adoption. That is a legitimate reason, but you need to plan for the extensibility debt you are taking on.
The second thing engineers miss is relay fallback readiness. Most teams test P2P connectivity in controlled environments where direct connections always succeed. In production, 10 to 15 percent of connections will fail and fall back to relay. If your relay capacity is not sized for that load, your system degrades under real traffic exactly when reliability matters most.
Memory bloat under many simultaneous connections is another operational pitfall that only shows up at scale. Unit tests will not catch it. Always run load tests with real traffic volumes before committing to a protocol stack.
Protocol choice is not a one-time decision. NAT behavior, regulatory requirements, and security standards will change. Build for extensibility from day one.
Take the next step with cutting-edge overlay networking
If you are ready to experiment with protocol wrapping in real-world agent overlays, here is where to start.

Pilot Protocol gives you a production-ready overlay network built specifically for AI agents and distributed systems. You get encrypted tunnels, NAT traversal, virtual addresses, and mutual trust establishment out of the box, with support for wrapping HTTP, gRPC, and SSH inside the overlay. No central broker required. The protocol overlay guide walks you through the core concepts and gets you connected in minutes. Whether you are building autonomous agent fleets, secure data pipelines, or cross-cloud orchestration, Pilot Protocol gives you the infrastructure to move fast without compromising on security or flexibility.
Frequently asked questions
What is protocol wrapping in networking?
Protocol wrapping is a method where one protocol’s data is enclosed inside another protocol’s packet to enable communication over networks that don’t natively support the original protocol. It is the foundational mechanism behind VPNs, overlays, and modern P2P agent networks.
How does protocol wrapping improve peer-to-peer agent communication?
It allows agents to connect across NATs and firewalls securely by encapsulating protocols, increasing connection success rates and flexibility. UDP overlays enable P2P agents to establish connections 11 times faster than HTTP and consume less memory.
What’s the difference between VXLAN and Geneve?
VXLAN is a popular encapsulation standard with a fixed 24-bit VNI and no native metadata extensibility. Geneve TLV enables extensibility for future metadata, making it the better choice for systems that need to adapt over time.
How do anonymity wrappers protect privacy in P2P communication?
They conceal protocol metadata and minimize message size, achieving strong forward secrecy even against state exposure. Anonymity wrappers provide strong metadata privacy, forward secrecy, and reduce message size compared to Sealed Sender.


