Virtual network addresses for secure decentralized AI
Virtual network addresses for secure decentralized AI
TL;DR:
- Virtual addresses in software-defined networks enable scalable, isolated, and location-independent agent communication.
- Crypto-derived addresses allow decentralized peer discovery, NAT traversal, end-to-end encryption, and secure identity.
- Proper planning of CIDR blocks and relay fallback mechanisms prevent silent routing failures and network outages.
The most secure autonomous agent fleets running today often never assign IP addresses the traditional way. That’s not a bug. It’s a deliberate design choice. Logical IP addresses assigned within software-defined networks are fundamentally different from the physical IPs bound to hardware NICs. For AI engineers building distributed agent systems, mistaking one for the other creates real problems: routing conflicts, NAT failures, broken peer discovery, and exposure of physical network topology. This article unpacks how virtual network addresses actually work, why they’re purpose-built for autonomous agent fleets, and what practical pitfalls you need to avoid before they cost you a production outage.
Table of Contents
- What is a virtual network address?
- How virtual addresses power decentralized AI agent networks
- Mechanics of virtual address assignment and routing
- Challenges, edge cases, and practical lessons
- Why crypto-derived virtual addresses are essential for autonomous agent fleets
- Build secure, scalable agent fleets with Pilot Protocol
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Logical address isolation | Virtual network addresses add a layer of isolation and routing flexibility crucial for agent security and scalability. |
| Crypto-derived addresses | Agent-centric overlays use cryptographic keys to deterministically assign unique, secure virtual addresses. |
| NAT and compatibility | Overlays handle NAT traversal and legacy app compatibility but require proactive design for relays and address overlaps. |
| Centralized vs decentralized | Decentralized assignment outperforms cloud VCNs for peer-to-peer flexibility in global agent fleets. |
What is a virtual network address?
A virtual network address is a logical IP assigned within a software-defined network, not to a physical interface on a machine. Think of it as an address that exists in software and can be moved, replicated, or derived without touching any hardware configuration. Cloud VCNs and overlay networks use this model to provide isolation, scalability, and rerouting benefits that physical addressing simply cannot deliver.
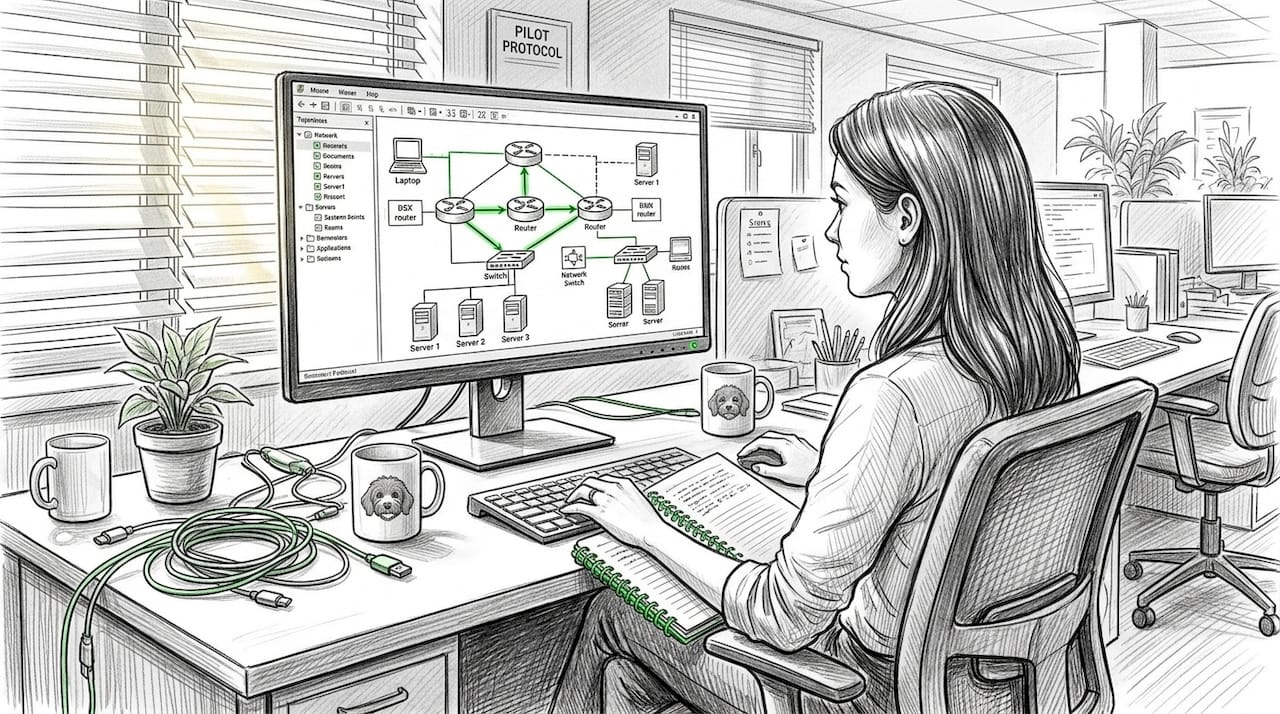
Where do virtual addresses appear in practice?
- Cloud VCNs (Virtual Cloud Networks): AWS VPCs, Azure VNets, and Oracle VCNs assign virtual IPs to instances inside isolated routing domains.
- Overlay networks: Tools like ZeroTier, WireGuard meshes, and overlay networking solutions create a logical network on top of any physical underlay.
- Agent fleets: Each AI agent gets a stable virtual address, independent of where it physically runs or which cloud region hosts it.
The key properties that make virtual addresses useful for distributed systems include:
- Isolation: Agents in one virtual network can’t directly reach agents in another without explicit peering or routing rules.
- Scalability: You can spin up thousands of agents with unique addresses without exhausting physical address space or reconfiguring routers.
- Rerouting: If an agent moves between data centers or cloud regions, its virtual address stays the same while the underlay routing updates silently.
- No hardware dependency: Virtual addresses aren’t tied to any NIC, MAC address, or physical slot.
One common misconception is that virtual addresses eliminate CIDR (Classless Inter-Domain Routing) overlap problems. They don’t. When you peer two VCNs or merge two overlay networks, overlapping address blocks cause silent routing failures that are notoriously hard to debug. Following network segmentation best practices and planning your IP blocks before you deploy saves hours of troubleshooting later.
Pro Tip: Always check for CIDR overlaps before configuring VCN peering or overlay merges. Use tools like "ipcalc` or built-in cloud validation checks to catch conflicts at design time, not at 2 a.m. during an incident.
How virtual addresses power decentralized AI agent networks
With a foundational definition in place, let’s see what makes virtual addressing uniquely powerful for distributed AI and autonomous agent networking.
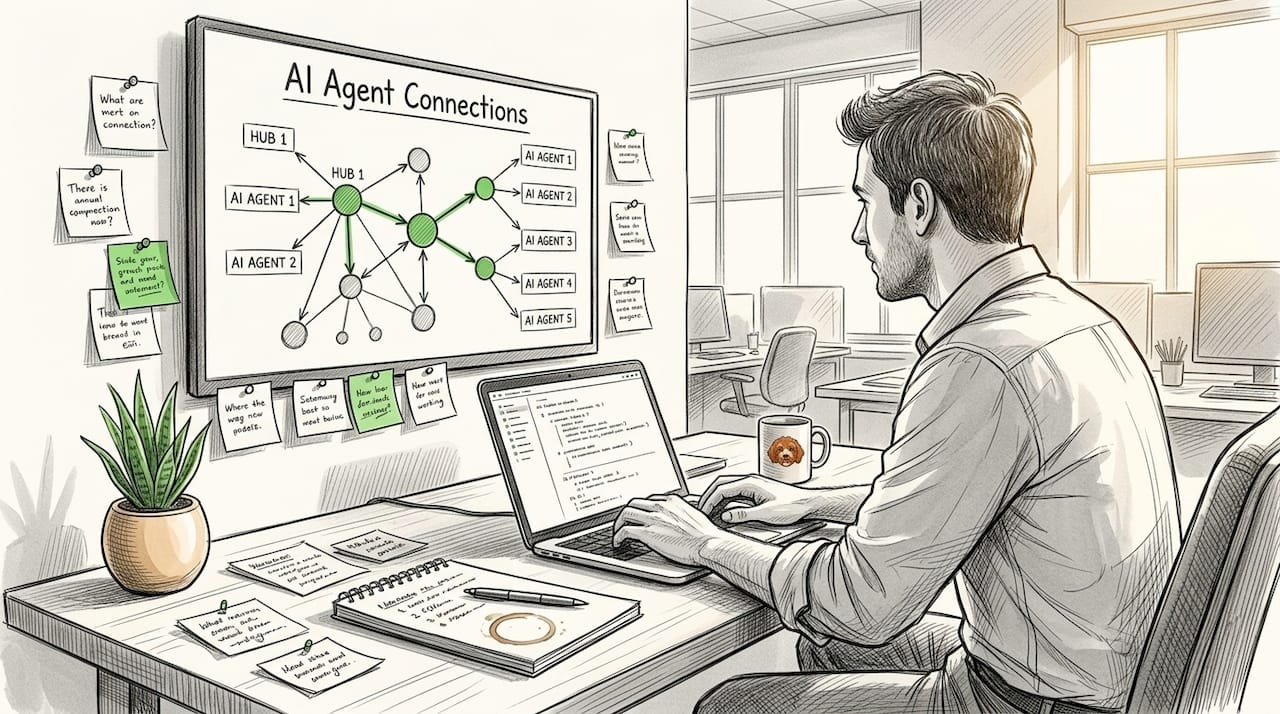
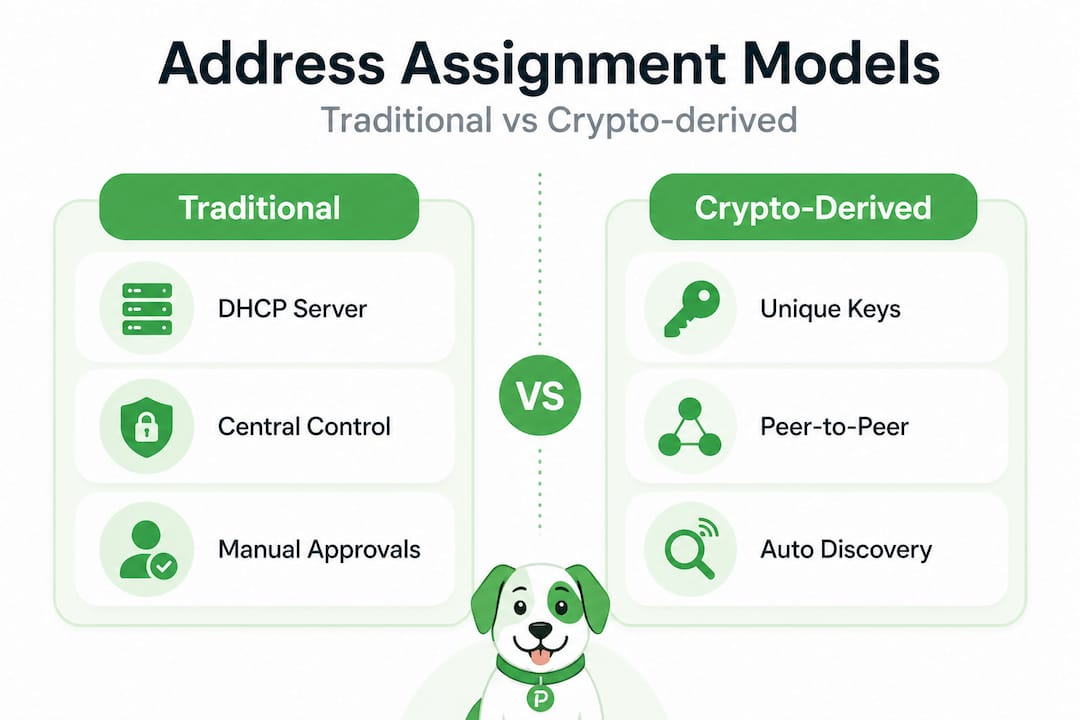
Centralized systems rely on a DHCP server or cloud control plane to hand out addresses. That works well until your agents span multiple clouds, edge nodes, and peer-to-peer links where no single authority exists. Decentralized overlays solve this differently: they derive virtual addresses from cryptographic identities.
FIPS (Fully Isolated P2P Spaces) maps a Nostr public key (npub) to an fd00::/8 IPv6 address via a TUN interface. No DHCP. No central registry. Each agent derives its own address deterministically from its public key, making it globally unique and cryptographically verifiable. ZeroTier takes a similar approach with its 40-bit node ID derived from a cryptographic identity, then uses 6PLANE and /80 per-host delegation for Kubernetes pod networking, giving each container a stable, routable IPv6 address without any manual configuration.
| Approach | Address assignment | Authority | NAT traversal | Use case |
|---|---|---|---|---|
| Cloud VCN | DHCP / control plane | Centralized | Not needed (private) | Single-cloud workloads |
| ZeroTier | Crypto ID derived | Decentralized | Built-in (UDP hole punch) | Multi-cloud, edge agents |
| FIPS / npub | Public key hash | Fully self-sovereign | TUN + relay | P2P AI agent fleets |
| WireGuard mesh | Static config | Manual / semi-central | Partial | Security-focused overlays |
For AI agent fleets specifically, crypto-derived addresses deliver four compounding benefits:
- Zero-config peer discovery: Agents find each other using their address as identity. No DNS, no service registry.
- NAT traversal: The overlay protocol handles hole punching so agents behind firewalls can still connect directly.
- End-to-end encryption: Because the address is derived from a public key, the transport layer can authenticate and encrypt without a separate PKI (Public Key Infrastructure).
- Isolation by default: Agents only connect to peers whose identities are explicitly authorized, reducing lateral movement risk.
“Overlay networks abstract physical topology, using underlay for transport while providing stable virtual IPs.” This is exactly the property that makes them suitable for AI network tunnels where physical topology changes constantly as agents scale up and down.
Pro Tip: Crypto-derived addresses ensure each agent is uniquely identified and securely discoverable with no DHCP required. Store the private key securely and your agent’s network identity is portable across any cloud, region, or hardware.
Mechanics of virtual address assignment and routing
Understanding why virtual address assignment matters is vital, but how does it all work behind the scenes, from ID derivation to secure routing?
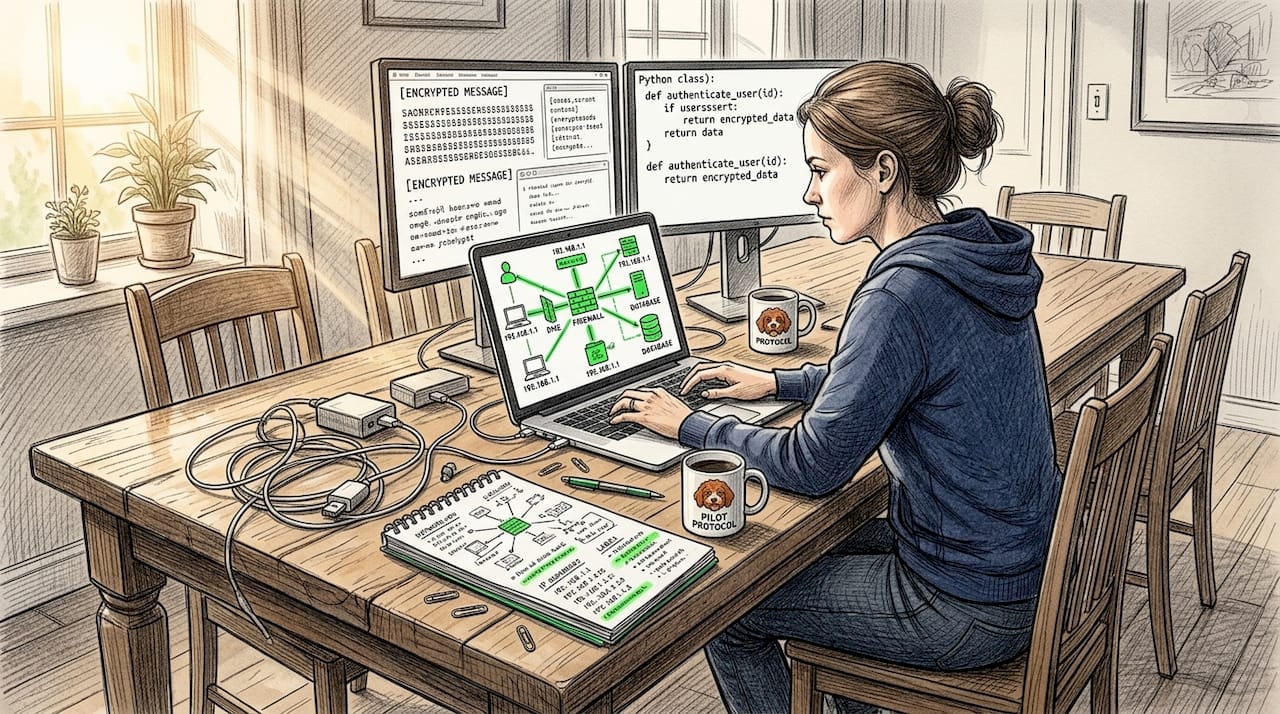
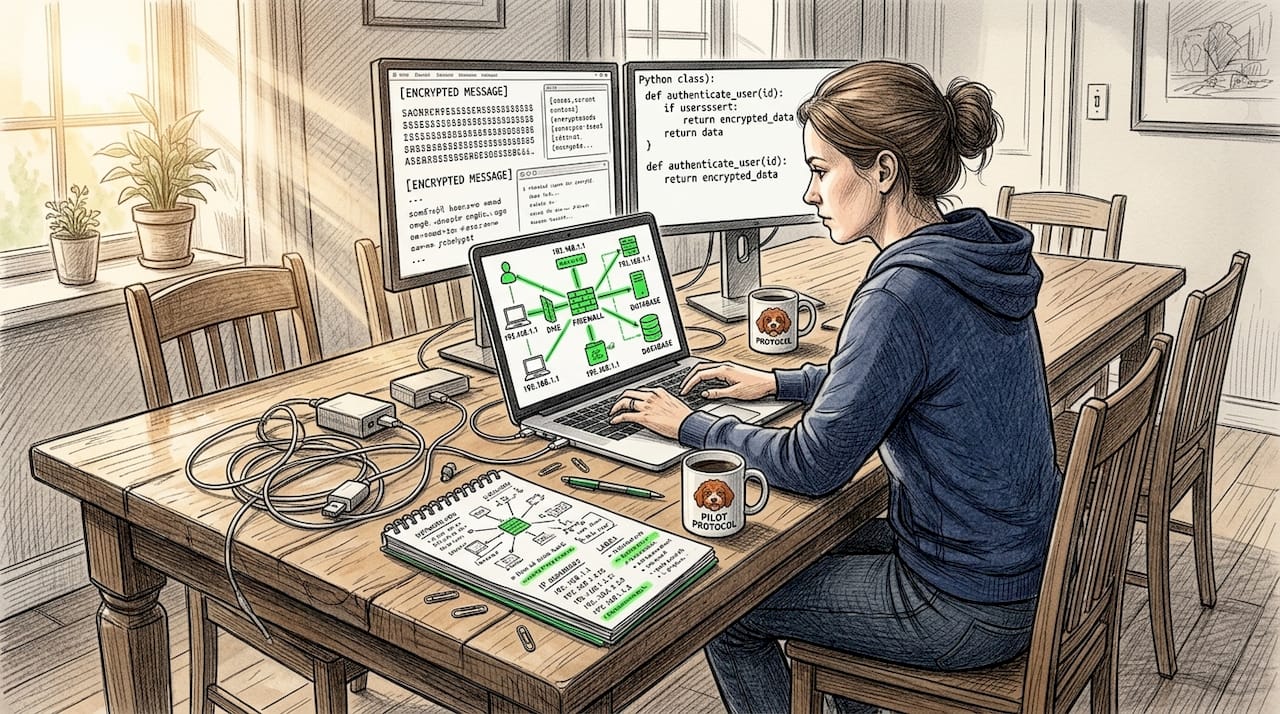
Here’s the step-by-step process for how a decentralized overlay assigns and uses a virtual address:
- Identity generation: The agent generates a cryptographic keypair (e.g., Ed25519 or Curve25519). The public key becomes the basis for its network identity.
- Address derivation: A deterministic hash (e.g., Blake3(pubkey) in meshguard) maps the public key to a specific IP range like
10.99.x.y. No collisions, no coordination needed. - TUN interface setup: The overlay creates a virtual TUN (network tunnel) interface on the agent’s host and assigns the derived IP to it. The OS routes traffic for that IP through the TUN device.
- Encapsulation: Outbound packets are encapsulated using VXLAN-like framing (ZeroTier calls this VL2, its virtual Layer 2), wrapped in UDP, and sent over the physical underlay network.
- Peer-to-peer transport (VL1): ZeroTier’s VL1 layer handles direct peer-to-peer UDP delivery between nodes, including secure protocol designs for authenticated sessions.
- NAT traversal: If agents are behind NATs, the overlay uses UDP hole punching. Both peers signal through a coordination point, then send simultaneous UDP packets to open a path through each NAT. If that fails (symmetric NAT), traffic falls back to an encrypted relay.
- Route table updates: Each agent maintains a local route table mapping virtual IPs to peer endpoints. This updates dynamically as peers join, leave, or move.
| Layer | Function | Protocol example |
|---|---|---|
| VL1 (transport) | Peer discovery, NAT traversal, relay fallback | ZeroTier VL1, QUIC |
| VL2 (virtual L2) | Ethernet frame encapsulation | VXLAN-like, Geneve |
| Crypto identity | Address derivation, auth | Ed25519, Blake3 |
| TUN interface | OS-level virtual NIC | Linux TUN/TAP |
| Application | Your AI agent workload | HTTP, gRPC, SSH |
Peer-to-peer overlays consistently outpace centralized VPNs for latency and scalability in multi-region deployments. Centralized VPN hubs become bottlenecks as agent counts grow; direct P2P paths scale linearly because each new peer adds its own forwarding capacity.
One subtlety worth understanding: deterministic address mapping means two agents with different keys will never collide in the same overlay. But if you merge two overlays that independently derived addresses from the same IP block, you get conflicts at the routing layer even if the crypto identities are unique. This is why the address block (e.g., which /8 or /24 you use) still matters in overlay security design.
Challenges, edge cases, and practical lessons
To make these concepts real, let’s surface the practical stumbling blocks and how expert practitioners prevent network headaches and outages.
Building virtual-addressed agent networks at scale surfaces a predictable set of problems. Here are the ones that cause the most incidents:
-
CIDR overlap in merged overlays: If you’re peering two VCNs or connecting two independently deployed overlay networks, overlapping CIDR blocks cause packets to route to the wrong destination with no obvious error. This is especially common when teams deploy the same default
10.0.0.0/8range in separate environments and then try to connect them. According to libp2p’s documented issues, CIDR overlap in VCN peering requires non-overlapping blocks to avoid silent routing failure. -
Symmetric NAT failures: UDP hole punching works well for full-cone and port-restricted NATs. It fails completely against symmetric NATs, where each outbound connection gets a different external port. Many enterprise and carrier-grade NATs use symmetric mode. Without a relay fallback, your agents simply can’t connect. Addressing this in your problem statement design before deployment is critical.
-
IPv6 and IPv4 dual-stack issues: Crypto-derived addresses often use IPv6 ranges (e.g.,
fd00::/8). If your legacy services only support IPv4, you need address mapping or protocol translation in the overlay. Libp2p’s circuit relay has known issues with IPv6/IPv4 dual-stack handoffs that can silently drop connections. -
Protocol compatibility: Modern overlays use multiaddrs (a libp2p addressing scheme like
/ip4/192.0.2.1/tcp/4001/p2p/Qm...) which legacy applications don’t understand. IP tunneling through a TUN interface solves this by presenting a normal IP address to the application, but adds one more abstraction layer to debug when things go wrong. -
Key management complexity: When addresses derive from keys, losing a private key means losing that agent’s network identity permanently. You need a key rotation and backup strategy before you scale up. Neglecting this is the distributed systems equivalent of throwing away your server’s SSH key. Check zero trust network policies for agent key management patterns.
-
Policy enforcement gaps: Virtual addresses provide isolation, but you still need explicit policy-based security rules to control which agents can initiate connections. Address-based isolation alone isn’t access control.
Pro Tip: Design for fallback relay mechanisms from the start. Don’t assume direct NAT punching always works. Build relay capacity into your infrastructure budget and test against symmetric NAT environments in staging before your agents hit them in production.
Why crypto-derived virtual addresses are essential for autonomous agent fleets
At this point, you can see how virtual addressing works technically. But field experience teaches something that specs don’t always capture: centralized address assignment is not just inconvenient for large agent fleets, it’s a structural bottleneck.
When you run dozens of agents, a central DHCP server is manageable. When you run thousands of agents across multiple clouds, edge nodes, and customer premises, that central server becomes a single point of failure, a scaling ceiling, and a security target simultaneously. The agents that need to coordinate most urgently (during an outage or an adversarial event) are exactly the agents that can’t reach the coordinator.
Crypto-derived addresses from FIPS and ZeroTier’s 40-bit ID model solve this by moving trust into the cryptographic layer. Each agent carries its own credential. It doesn’t need permission to exist on the network. It just needs peer agents to recognize its key. That’s a fundamentally more resilient architecture for autonomous systems.
There’s a harder truth here too. Teams that start with centralized assignment often convert later, under pressure, when scaling failures force their hand. That conversion is painful because it requires re-addressing running agents and updating all the routing tables that reference old IPs. Starting with crypto-derived addresses means your architecture scales gracefully from the first agent to the millionth without a flag day re-numbering event.
Policy-driven membership (where an agent’s key must appear in an authorized list before it can join the overlay) gives you the access control layer that pure address derivation lacks. Combine that with zero trust agent networking principles and end-to-end encryption, and you have a fleet that is both self-organizing and genuinely secure. That combination is not achievable with DHCP and a traditional VPN.
Build secure, scalable agent fleets with Pilot Protocol
If you’re ready to apply these principles in your distributed AI systems, Pilot Protocol gives you a direct path from concept to running agent network.

Pilot Protocol is built specifically for AI agent fleets that need P2P networking with persistent virtual addresses, encrypted tunnels, NAT traversal, and mutual trust establishment. It handles the hard parts: crypto-derived addressing, relay fallback, and cross-cloud routing, so your team focuses on agent logic rather than network plumbing. You can wrap your existing HTTP, gRPC, or SSH traffic inside the overlay without changing your application code. Explore the protocol specification to see exactly how address assignment and encapsulation work, or start with the CLI and Python/Go SDKs to connect your first agent in minutes.
Frequently asked questions
How do virtual network addresses improve security in AI agent fleets?
Virtual addresses isolate agents into logical network segments and support end-to-end encryption tied to cryptographic identity, meaning hop-by-hop and E2E encryption with Noise IK/XK protocols can authenticate each connection without exposing physical network details or device locations.
Can virtual addresses work across cloud, edge, and peer-to-peer environments?
Yes. Modern overlays assign logical IPs that are independent of physical infrastructure, so the same virtual address works whether the agent runs on AWS, an edge node, or a bare-metal peer, provided CIDR blocks are planned to avoid overlap across environments.
What are the biggest network failure risks with virtual addressing?
CIDR overlap and symmetric NAT are the two most common causes of silent routing failures. Overlapping address blocks send packets to wrong destinations, while symmetric NATs block direct hole punching and require relay infrastructure to maintain connectivity.
Are crypto-derived addresses compatible with legacy apps and protocols?
Yes. Through IP tunneling over TUN interfaces and address mapping layers, legacy applications see a normal IPv4 or IPv6 address and operate without modification, while the overlay handles all the cryptographic identity and routing complexity underneath.
Recommended
- Persistent network addressing for secure AI systems
- Cloud networking: Secure peer-to-peer for distributed AI
- Decentralized networking: P2P solutions for AI architectures
- AI networking best practices for secure, scalable systems
- Diploma of Artificial Intelligence Australia | Get AI Qualified Online | CTDI — Canterbury Training and Development Institute