Overlay networking: Secure AI agent communication explained
Overlay networking: Secure AI agent communication explained
TL;DR:
- Overlay networks enable secure, persistent, and flexible communication for distributed AI agents.
- Control and data planes separate endpoint discovery and packet forwarding, improving scalability.
- Protocol choices and topology patterns impact performance, resilience, and operational complexity.
Networking is not just about physical cables and IP addresses. Most distributed systems developers spend time optimizing underlay infrastructure while overlooking the layer that actually enables secure, flexible agent communication: the overlay network. Overlay networking lets your AI agents find each other, exchange data, and maintain trust regardless of the underlying physical topology. This guide covers the core concepts, protocols, topology patterns, and performance trade-offs you need to design and deploy secure overlays for autonomous agent fleets and distributed AI systems.
Table of Contents
- What is overlay networking? Core concepts and encapsulation
- Control and data planes: How overlays manage complexity
- Common overlay protocols: VXLAN, GRE, Geneve and their trade-offs
- Structured and unstructured overlays: Routing patterns for distributed systems
- Performance in practice: Benchmarks, trade-offs, and secure overlays for AI agents
- Our perspective: What most guides miss about overlay networking for agents
- Build secure, direct overlays for your AI agents with Pilot Protocol
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Encapsulation is essential | Overlay networking wraps packets with headers and encryption, enabling secure, transparent agent communication. |
| Control/data plane separation | Dividing logic and packet forwarding simplifies scalable overlays in distributed applications. |
| Choose the right protocol | Protocol options like VXLAN, GRE, and Geneve each address specific performance and compatibility needs. |
| Topology impacts efficiency | Structured vs unstructured overlays balance lookup speed, resilience, and scalability for AI agents. |
| MTU and performance tuning | Correct MTU settings and protocol selection prevent silent failures and maximize overlay throughput. |
What is overlay networking? Core concepts and encapsulation
An overlay network is a virtual network built on top of an existing physical or logical network, called the underlay. You define logical connections between nodes that may be physically distant or separated by NAT boundaries, firewalls, or different cloud providers.
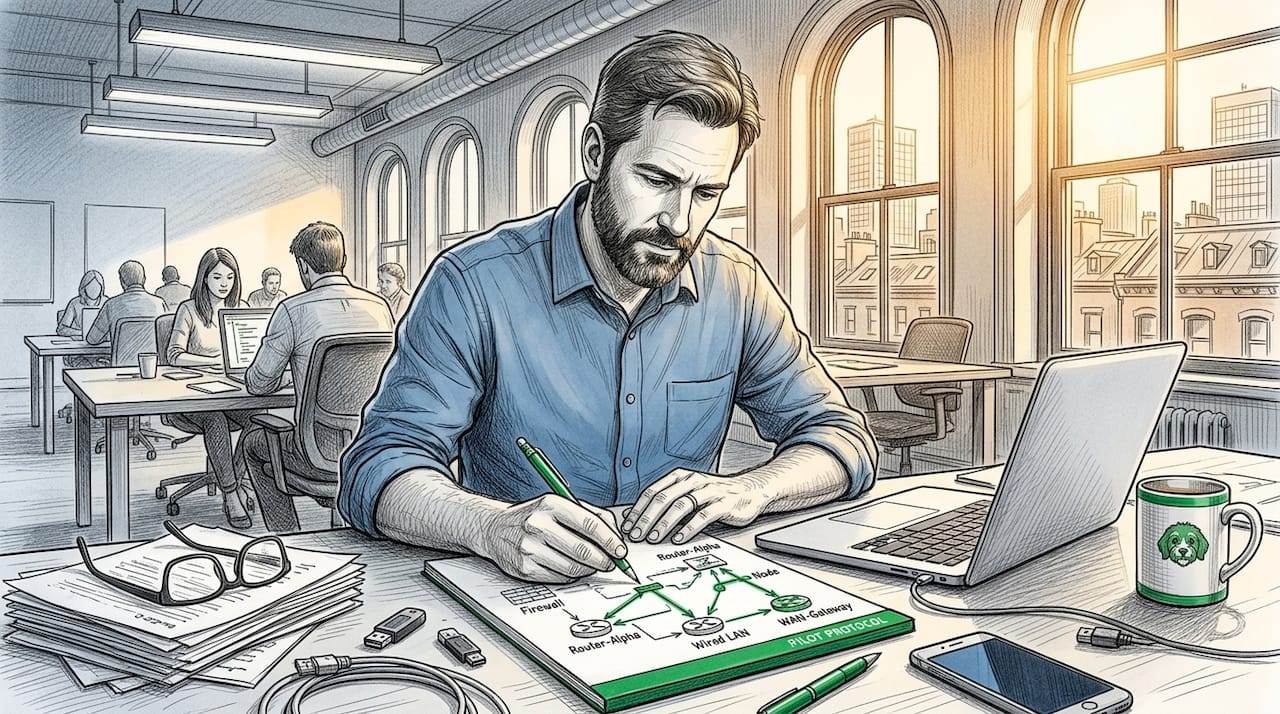
The core mechanism is encapsulation: packets wrapped with overlay headers such as VXLAN adding Ethernet, IP, UDP, and VXLAN headers, often with encryption, while the underlay treats them as normal traffic. The underlay never needs to understand the overlay’s addressing scheme. This separation is what gives overlays their power.
Common encapsulation formats include:
- VXLAN: Wraps Layer 2 frames in UDP, enabling Ethernet segment extension across IP networks
- GRE: A simpler IP-in-IP tunnel, Layer 3 focused, with lower overhead
- Geneve: Extensible via TLV metadata fields, designed for modern virtualized environments
- WireGuard: Lightweight, cryptographically strong, gaining traction in agent networking
For AI agent communication, overlay protocol encapsulation provides a critical advantage. Your agents get stable virtual addresses that persist even when physical endpoints change, move between clouds, or reconnect after failures. The overlay handles address resolution and path selection transparently.
Protocol wrapping in AI systems also means you can carry HTTP, gRPC, or SSH traffic inside the overlay tunnel without modifying the application layer. Agents communicate using familiar protocols while the overlay handles encryption, NAT traversal, and routing.
| Feature | Without overlay | With overlay |
|---|---|---|
| Agent addressing | Tied to physical IP | Persistent virtual address |
| NAT traversal | Manual port forwarding | Automatic punch-through |
| Encryption | Application-level only | Tunnel-level, end-to-end |
| Multi-cloud reach | Complex routing rules | Transparent via overlay |
Understanding overlay network mechanics at this level helps you design agent networks that are resilient to infrastructure changes.
Pro Tip: Always monitor MTU settings in your overlay deployment. Encapsulation adds header bytes, so if your underlay MTU is 1500 bytes and your overlay adds 50 bytes of headers, you will silently drop packets unless you adjust MTU values or enable jumbo frames on the underlay.
Control and data planes: How overlays manage complexity
With a foundation in how overlays package data, the next step is to understand how they orchestrate communication.
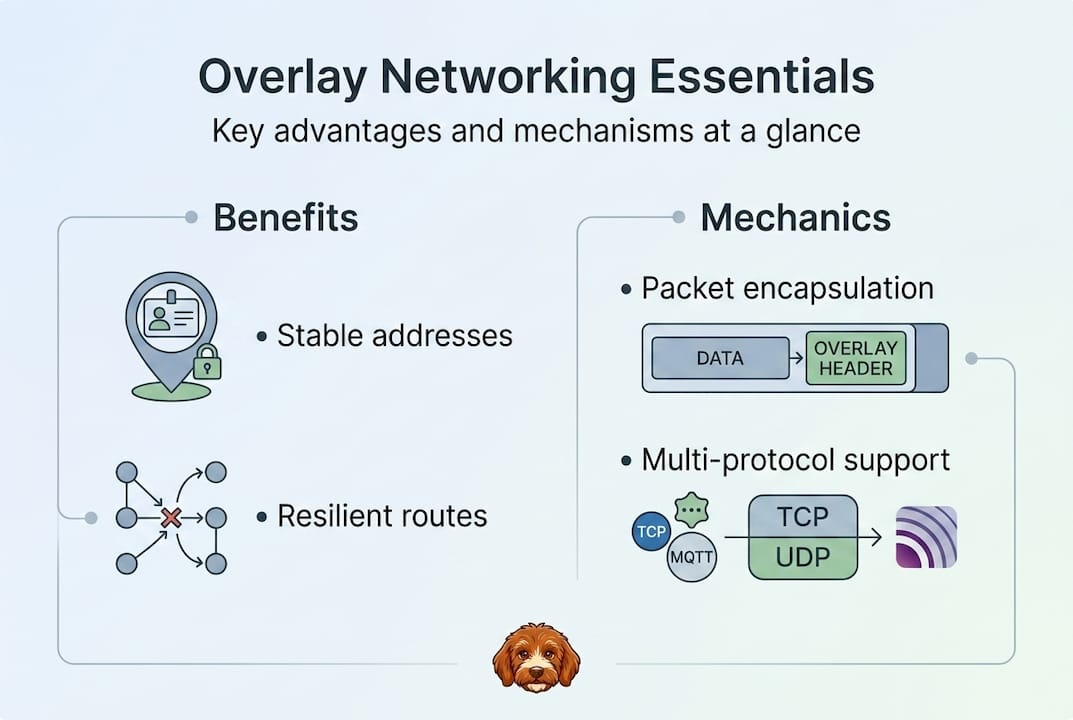
Every overlay network separates two distinct functions: the control plane and the data plane. Control plane handles endpoint discovery, route advertisement, and policy distribution, while the data plane performs the actual encapsulation and decapsulation of packets. This separation is what makes overlays scalable.
Here is how data flows through a typical overlay network:
- Agent A sends a request to Agent B using Agent B’s virtual overlay address
- Control plane lookup resolves the virtual address to a physical underlay endpoint
- Encapsulation wraps the original packet with overlay headers at the source node
- Underlay transport carries the encapsulated packet across physical infrastructure
- Decapsulation strips overlay headers at the destination node
- Agent B receives the original packet as if it arrived on a local network
The control plane is where control and data plane automation becomes critical for AI agent fleets. When you have hundreds of agents joining and leaving dynamically, manual route management is not feasible. Automated control planes handle discovery, policy enforcement, and failover without human intervention.
| Responsibility | Control plane | Data plane |
|---|---|---|
| Endpoint discovery | Yes | No |
| Route advertisement | Yes | No |
| Policy enforcement | Yes | Partial |
| Packet encapsulation | No | Yes |
| Traffic forwarding | No | Yes |
| Latency sensitivity | Low | High |
“Separating control and data planes simplifies operations by letting you update routing logic and policies without touching the forwarding path, which is essential for maintaining uptime in production agent networks.”
Protocol overlays explained in the context of AI systems show that the control plane is also where trust gets established. Agents authenticate, exchange certificates, and register their virtual addresses through the control plane before any data flows. This is fundamentally different from traditional networking, where trust is often assumed within a subnet.
Multi-cloud overlays rely heavily on a robust control plane to maintain consistent routing tables across AWS, GCP, Azure, and on-premises nodes simultaneously. Without it, cross-cloud agent communication becomes fragile and hard to debug.
Common overlay protocols: VXLAN, GRE, Geneve and their trade-offs
To choose the right overlay, you need to know the strengths and limits of key protocols.
Common protocols include VXLAN using UDP port 4789 with a 24-bit VNI supporting 16 million segments and 50-byte overhead, GRE using IP protocol 47 with 24-byte overhead and a Layer 3 focus, and Geneve using UDP port 6081 with TLV extensions for metadata flexibility.
| Protocol | Transport | Port | Overhead | VNI/Segments | Best for |
|---|---|---|---|---|---|
| VXLAN | UDP | 4789 | ~50 bytes | 16M (24-bit) | Large-scale L2 extension |
| GRE | IP | Protocol 47 | ~24 bytes | N/A | Simple L3 tunneling |
| Geneve | UDP | 6081 | Variable | Extensible | Cloud-native, metadata-rich |
| WireGuard | UDP | Custom | ~60 bytes | N/A | Encrypted agent tunnels |
When selecting a protocol for your agent network, consider these factors:
- Latency requirements: GRE has lower overhead but lacks built-in encryption
- Hardware offload support: VXLAN is widely supported in NIC offload engines, reducing CPU cost
- Metadata needs: Geneve’s TLV fields let you carry agent identity, policy tags, or routing hints inside the tunnel header
- Encryption: WireGuard provides strong cryptographic guarantees with minimal configuration
- Compatibility: VXLAN is the most widely supported across hypervisors, switches, and cloud providers
MTU edge cases with encapsulation overhead are a real operational risk. VXLAN adds roughly 50 bytes and Geneve with IPv6 can add up to 70 bytes, requiring underlay MTU of at least 1450 to 1500 bytes. Misconfigurations cause silent drops if Path MTU Discovery is blocked by firewalls, which is common in enterprise environments.
For AI agent communication specifically, look at HTTP services over encrypted overlays to understand how protocol choice affects end-to-end latency for request-response workloads.
Pro Tip: Always coordinate MTU settings between your overlay and underlay before deploying agents in production. Run a simple test: send a 1400-byte ping with the DF bit set between two overlay nodes. If it fails, you have an MTU problem that will silently break agent communication under load.
Structured and unstructured overlays: Routing patterns for distributed systems
Beyond the basic protocols, overlay topology shapes actual communication efficiency and resilience.
Structured overlays use DHTs like Chord and Kademlia with O(log N) routing via consistent hashing, finger tables, and k-buckets. Unstructured overlays use gossip protocols or flooding, which are resilient but less efficient for lookups. The choice between them has major implications for how your agents discover each other and share data.
Structured overlays organize nodes in a defined topology. Chord arranges nodes in a ring and uses finger tables to route lookups in O(log N) hops. Kademlia uses XOR distance metrics and k-buckets, which is the basis for BitTorrent’s DHT and IPFS. These approaches scale well and provide predictable lookup times even with thousands of nodes.
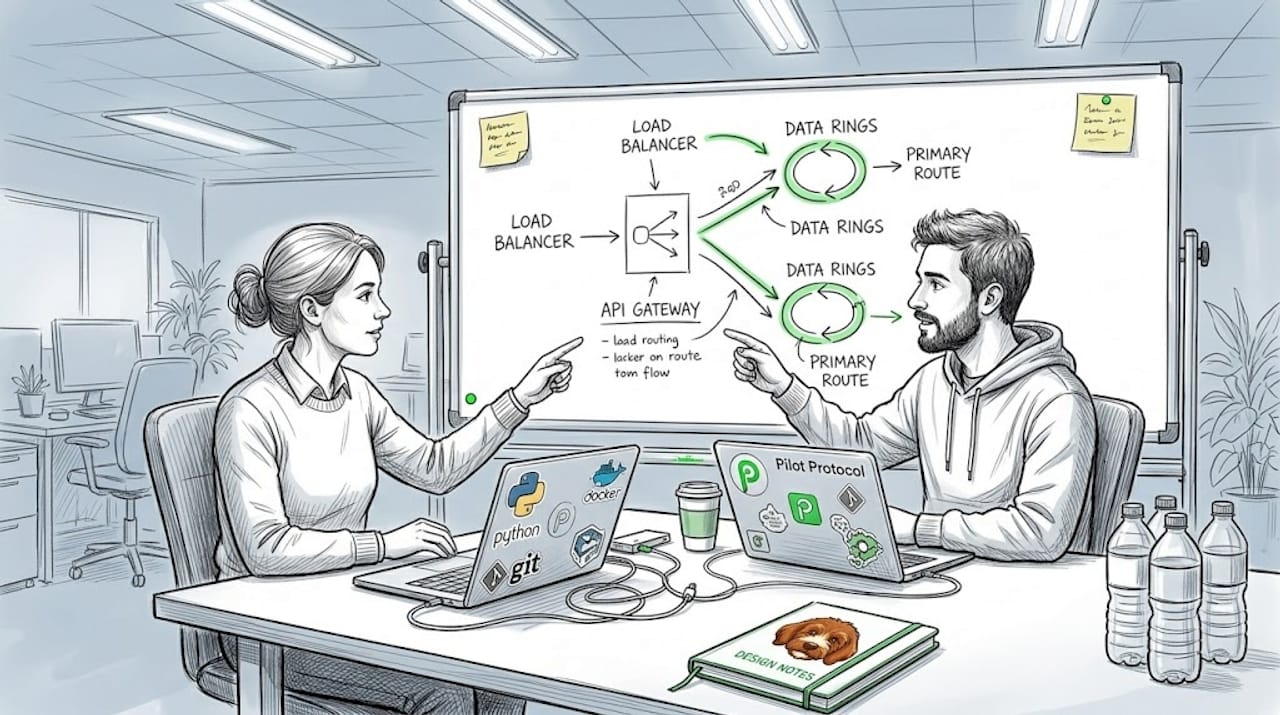
Unstructured overlays make no assumptions about topology. Gossip protocols spread information by having each node randomly share state with neighbors. Flooding broadcasts queries to all reachable nodes. Both approaches are highly resilient to node churn but can generate significant traffic at scale.
| Property | Structured (DHT) | Unstructured (Gossip/Flood) |
|---|---|---|
| Lookup speed | O(log N) | O(N) worst case |
| Scalability | High | Moderate |
| Churn resilience | Moderate | High |
| Implementation complexity | Higher | Lower |
| Bandwidth efficiency | High | Lower |
| Decentralization | Full | Full |
When does each approach fit your agent network?
- Use structured overlays when you need fast, deterministic key-value lookups across a large agent fleet
- Use unstructured overlays when resilience to node failures matters more than lookup efficiency
- Use gossip protocols for propagating configuration updates, health status, or capability announcements across agents
- Use DHTs when agents need to locate specific data or services without a central registry
“The trade-off between scalability, resilience, and lookup performance is not a problem to solve once. It is a design constraint you revisit as your agent fleet grows and your communication patterns evolve.”
For most production AI agent deployments, a hybrid approach works best. Use a DHT for service discovery and a gossip layer for health propagation. This gives you efficient lookups with strong resilience against node churn.
Performance in practice: Benchmarks, trade-offs, and secure overlays for AI agents
After topology, practical performance numbers help you select and tune overlays for AI workloads.
Kubernetes CNI benchmarks show Cilium eBPF achieving roughly 39Gbps same-node and 9.8Gbps cross-node throughput, while Flannel VXLAN reaches about 35Gbps same-node and 8.2Gbps cross-node. P99 latency for Cilium is 0.8ms versus 1.8ms for Flannel. These numbers reflect real-world overlay performance in containerized environments similar to AI agent deployments.
| Implementation | Same-node throughput | Cross-node throughput | P99 latency |
|---|---|---|---|
| Cilium eBPF | ~39 Gbps | ~9.8 Gbps | 0.8 ms |
| Flannel VXLAN | ~35 Gbps | ~8.2 Gbps | 1.8 ms |
| WireGuard overlay | ~10-20 Gbps | ~5-8 Gbps | 1-3 ms |
| GRE tunnel | ~25-30 Gbps | ~7-9 Gbps | 1-2 ms |
Key factors that determine overlay performance in agent networks:
- Hardware offload: NIC offload for VXLAN encapsulation reduces CPU overhead significantly
- Underlay MTU: Larger MTU reduces per-packet overhead and improves throughput
- Protocol choice: eBPF-based overlays bypass kernel networking stack for lower latency
- Encryption cost: AES-NI hardware acceleration keeps encryption overhead minimal on modern CPUs
- Topology: Same-node communication should bypass the overlay entirely when possible
Security adds overhead, but the cost is manageable. AES-256-GCM with hardware acceleration adds roughly 5 to 10 percent CPU overhead compared to unencrypted tunnels. For AI agent workloads involving sensitive data, model weights, or inference results, this trade-off is almost always worth it.
Check out overlay benchmarking results for detailed comparisons specific to HTTP and UDP workloads over encrypted overlays.
Pro Tip: Test your overlay under real traffic patterns before final deployment. Synthetic benchmarks with iperf3 will not reveal issues like head-of-line blocking, connection state exhaustion, or MTU fragmentation that only appear under actual agent communication workloads.
Our perspective: What most guides miss about overlay networking for agents
Most overlay networking guides focus on protocol specs and configuration steps. They miss the operational reality of running overlays under production AI workloads.
The biggest gap we see is underlay health. Developers tune overlay parameters carefully but ignore packet loss, jitter, and asymmetric routing in the underlay. A 0.1 percent packet loss rate in the underlay can translate to significant retransmission overhead in the overlay, especially for latency-sensitive agent communication. Monitor your underlay actively, not just your overlay metrics.
The second gap is testing both control and data planes independently. Most teams test connectivity and call it done. But control plane failures, like a stale route advertisement or a failed endpoint registration, can cause agent communication to silently route to wrong destinations. Test your control plane’s behavior under node churn, network partitions, and policy updates separately from data plane throughput.
For truly decentralized agent networks, cryptographic primitives matter more than topology choices. A deep dive on overlay protocols shows that mutual authentication and encrypted tunnels eliminate the central trust bottleneck that breaks most overlay designs at scale. Emerging P2P overlays are moving toward fully cryptographic identity models, which is the right direction for autonomous agent fleets.
Build secure, direct overlays for your AI agents with Pilot Protocol
Ready to apply overlays in your own AI projects? Pilot Protocol is built specifically for the requirements this guide covers: encapsulation, control and data plane separation, NAT traversal, mutual authentication, and persistent virtual addressing for agent fleets.

You get encrypted peer-to-peer tunnels, automatic NAT punch-through, and support for wrapping HTTP, gRPC, and SSH inside the overlay without changing your application code. Pilot Protocol handles endpoint discovery and trust establishment so your agents can find and verify each other across clouds and regions. Explore direct P2P overlays to see how Pilot Protocol maps to everything covered in this guide and start building secure, scalable agent networks today.
Frequently asked questions
How does overlay networking differ from VPNs?
Overlay networking creates virtual networks independent of the physical layer, supporting dynamic discovery and decentralized architectures, while VPNs primarily provide secure point-to-point tunnels. Unlike VPNs, overlays like those using VXLAN encapsulation support millions of virtual segments and automated endpoint discovery without manual tunnel configuration.
What are the risks if overlay and underlay MTU values mismatch?
MTU mismatches cause silent packet drops when encapsulation overhead pushes packets beyond the underlay’s maximum size, especially when Path MTU Discovery is blocked by firewalls. This disrupts agent communication in ways that are hard to diagnose without specific MTU testing.
Which overlay topology suits large-scale agent-based AI systems: structured or unstructured?
Structured overlays like DHTs deliver O(log N) lookups and scale efficiently to thousands of agents, making them the better choice for large fleets that need fast service discovery. Unstructured topologies work better when resilience to node churn outweighs the need for efficient lookups.
What is the performance overhead of using overlay networks?
Overlay protocols add header overhead and some latency, but modern implementations keep the cost low. Cilium eBPF achieves roughly 39Gbps on-node throughput with P99 latency under 1ms, showing that well-implemented overlays are viable for high-performance agent communication workloads.


