Network security for multi-agent systems: Key strategies
Network security for multi-agent systems: Key strategies
TL;DR:
- Multi-agent systems enable rapid AI coordination but introduce significant network security risks with growing attack surfaces.
- Layered defense architectures, including runtime inspection, secure protocols, and hierarchical structuring, are essential for effective protection and visibility.
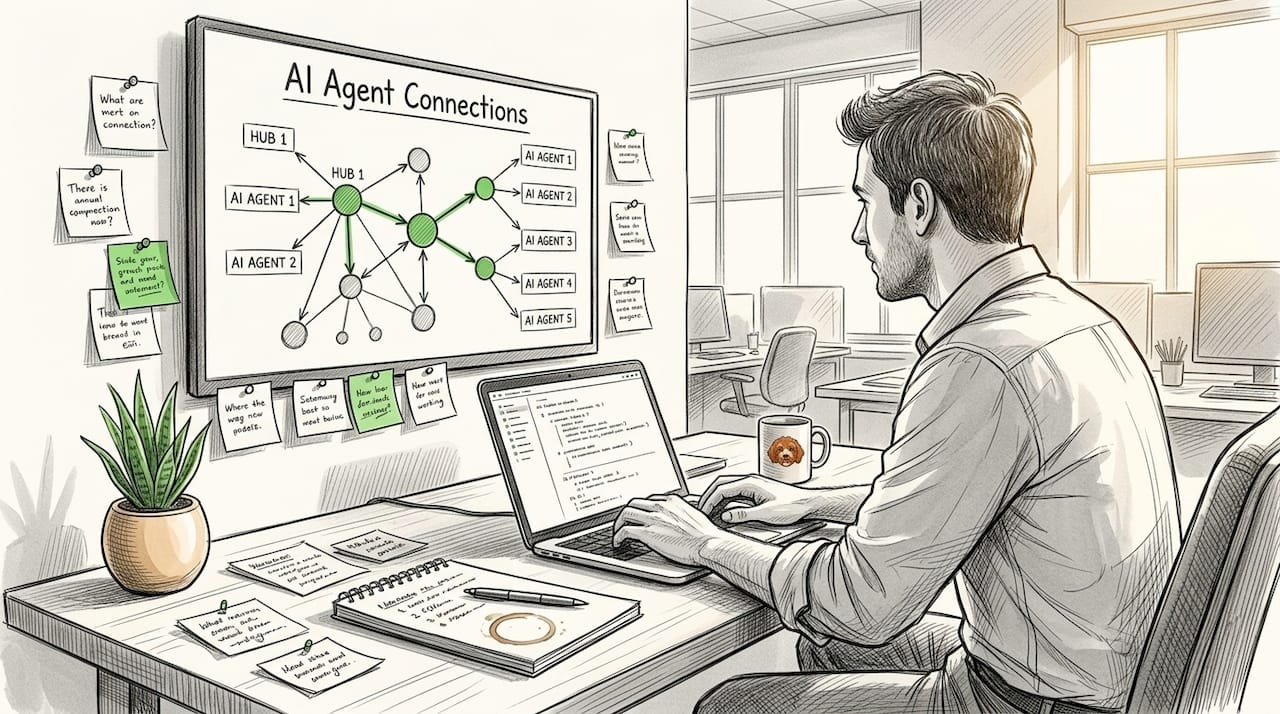
Multi-agent systems (MAS) let AI components coordinate at speeds and scales no human team can match, but that same speed creates network security risks that most teams discover too late. The attack surface grows with every new agent you add: each peer connection, tool call, and message hop is a potential entry point. Layered defensive architecture for multi-agent security requires visibility into agent behavior, intelligent runtime policies, and pre-execution defense that inspects prompts, outputs, and tool calls before a cascading compromise can take hold. This guide gives you the frameworks, protocols, and benchmarks to build that defense correctly from day one.
Table of Contents
- Understanding the network threats in multi-agent systems
- Layered defense architecture: Building visibility and guardrails
- Protocols and frameworks: Secure messaging and interoperability
- Architectural patterns: Hierarchical vs decentralized security
- Adaptive defense: Real-world performance and continuous validation
- What most developers overlook in multi-agent security
- Take the next step with secure peer-to-peer agent frameworks
- Frequently asked questions
Key Takeaways
| Point | Details |
|---|---|
| Layered defense matters | Combining visibility, pre-execution checks, and runtime policies helps prevent cascading attacks in agent networks. |
| Choose secure protocols | Frameworks like A2A, MCP, and BlockA2A enable robust, auditable communication between AI agents. |
| Architectural decisions impact risk | Hierarchical agent networks are more resilient to malicious compromise than linear or flat designs. |
| Benchmark and red-team often | Continuously test agent security through real-world adversarial scenarios and track metrics like compromise rate. |
Understanding the network threats in multi-agent systems
Traditional perimeter security was designed for environments where servers stay put and users are humans. Multi-agent systems break both assumptions. Agents are autonomous, they move tasks between services, spin up new connections dynamically, and often cross cloud boundaries. Static ACLs and firewall rules simply cannot keep pace.
The threat model for MAS networks includes adversaries that are not outside attackers probing a login page. They can be compromised agents already inside your network, injected instructions riding legitimate message channels, or coordinated replay attacks that mimic valid agent behavior. Understanding these vectors is the foundation of any solid defense.
Key attacker profiles and network risks you need to plan for:
- Malicious agents: A compromised agent acts as a trusted insider, relaying poisoned instructions to downstream peers.
- Trust amplification: One compromised node passes elevated permissions to a chain of agents that never independently validated the request.
- Replay attacks: Captured valid agent messages are re-sent to trigger repeated actions or escalate privileges.
- Compromise propagation: An initial breach spreads laterally across the agent mesh without triggering any perimeter alarm.
- Invisibility of failures: Agents silently fail or produce malicious outputs with no human-visible indicator.
Network-level risks in agent networks, including propagation, amplification, trust capture, and invisibility, require dedicated benchmarks for Agent Communication Integrity (ACI) such as compromise rate and attack chain length.
ACI is a measurement framework specifically designed for agent networks. It tracks how quickly a compromise spreads (compromise rate) and how many agents are affected before detection (chain length). Without these metrics, you are guessing at your actual risk exposure. You can learn more about agent network security challenges and P2P networking risks that apply directly to distributed agent deployments.
Layered defense architecture: Building visibility and guardrails
Visibility is not optional in agent networks. It is the first control that makes every other control useful. If you cannot observe what an agent sent, received, and executed, you cannot detect compromise, audit behavior, or tune policies.
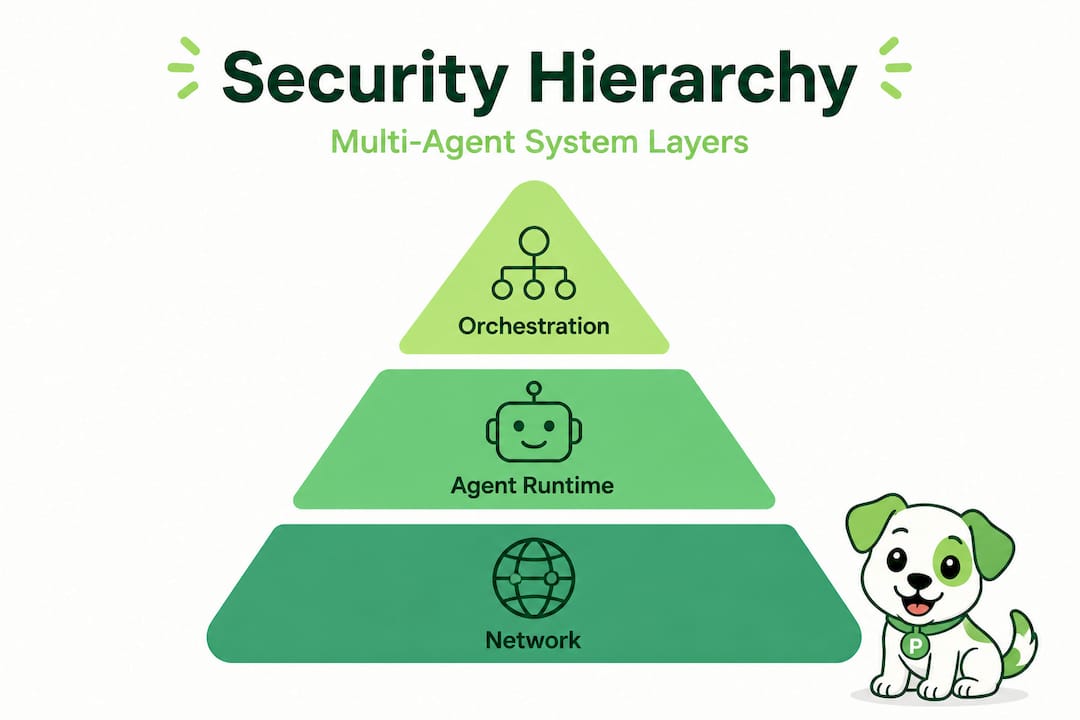
A layered defense stacks three control zones: the network layer, the agent runtime layer, and the orchestration layer. Each layer catches what the one above it misses.

| Defense layer | Key controls | What it catches |
|---|---|---|
| Network layer | Encrypted tunnels, NAT traversal, mutual TLS | Eavesdropping, spoofing, unauthorized connections |
| Agent runtime layer | Prompt inspection, output filtering, tool call restrictions | Injection attacks, policy violations, malicious outputs |
| Orchestration layer | Pub/sub audit hooks, auto-scaling limits, cache controls | Replay abuse, resource exhaustion, unauthorized orchestration |
Layered defensive architecture must include pre-execution runtime defense that inspects prompts, outputs, and tool calls to prevent cascading compromises before they propagate.
Runtime guardrails at the agent layer are where most teams underinvest. Inference-time policy enforcement means every prompt and every tool call is checked against a rule set before execution proceeds. This is not just about blocking bad inputs. It is about creating an auditable record that you can replay during incident response.
A practical defense workflow looks like this:
- Agent receives a task prompt from an orchestrator.
- Pre-execution inspection checks the prompt against known injection patterns and policy rules.
- If the prompt passes, the agent executes and its output is filtered before being forwarded.
- All steps are logged to an immutable audit trail indexed by agent ID and timestamp.
Cloud orchestration adds another control surface. Resilient pub/sub setups with audit hooks capture every message event. Auto-scaling rules prevent resource exhaustion attacks where a bad actor floods the system with agent spawn requests.
Pro Tip: Log MCP (Model Context Protocol) packet payloads at the inspection layer, not just connection metadata. Payload-level logs are what actually let you reconstruct an attack chain after the fact.
You can map these controls to practical infrastructure by reviewing visibility and runtime policies and reading the secure infrastructure best practices guide.
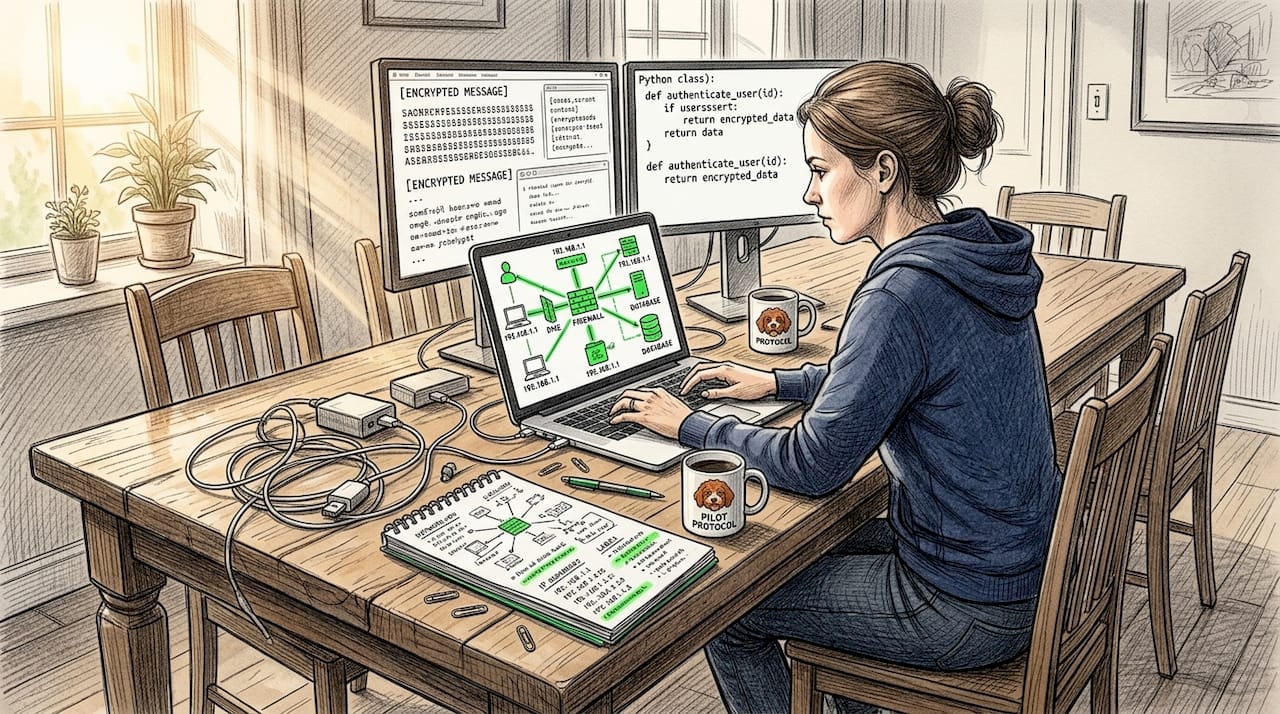
Protocols and frameworks: Secure messaging and interoperability
Choosing the right protocol for agent-to-agent messaging is one of the highest-leverage decisions you make in MAS design. The protocol determines what security guarantees you get at the message layer and how easily agents from different frameworks can interoperate.
Peer-to-peer coordination in multi-agent systems uses message passing without central control, and standardized protocols like MCP and A2A (Agent2Agent) enable secure agent-to-agent communication with defined semantics for task delegation and response handling.
| Protocol | Authentication | Auditability | Attack surface | Best use case |
|---|---|---|---|---|
| MCP | API key or OAuth | Partial (depends on implementation) | Tool call injection | Single-org agent orchestration |
| A2A | AgentCard identity | Task-level logs | AgentCard spoofing | Cross-org agent communication |
| BlockA2A | DIDs + blockchain | Full on-chain audit | Smart contract bugs | High-assurance interoperability |
| Noise Protocol | Ephemeral keys | Session-level | Key extraction | Low-latency P2P tunnels |
The BlockA2A framework uses decentralized identifiers (DIDs) for authentication, blockchain for auditability, and smart contracts for access control in agent-to-agent interoperability. Its Delegated Orchestration Engine (DOE) neutralizes certain replay and spoofing attacks with sub-second overhead, making it viable for production deployments where performance matters.
Common pitfalls teams hit when deploying these protocols:
- Skip AgentCard validation: Trusting an agent’s declared identity without cryptographic verification opens the door to spoofing. Always verify AgentCard signatures against a known root.
- Use static API keys for long-lived sessions: Rotate credentials per-session using ephemeral key exchanges like the Noise Protocol to limit the blast radius of a key leak.
- Ignore task replay: A2A tasks that carry no nonce or timestamp can be replayed by an attacker who captures a valid request. Add sequence numbers.
- Assume TLS is enough: TLS protects the transport layer, but it does nothing to stop an authorized agent from executing a malicious prompt. Layer it with runtime controls.
Steps to select and deploy a secure peer-to-peer protocol:
- Define your interoperability requirements. Cross-org communication needs stronger identity guarantees than single-org pipelines.
- Map your threat model to protocol capabilities using the table above.
- Add hybrid encryption if your threat model includes post-quantum adversaries. Combine AES-256 for speed with post-quantum cryptography (PQC) for forward secrecy.
- Implement nonce-based request signing to neutralize replay attacks at the message layer.
- Deploy audit hooks at both the sender and receiver ends so you have independent logs for forensics.
Pro Tip: Test AgentCard spoofing explicitly during your pre-launch red team. It is one of the most common A2A attack vectors and one of the easiest to overlook until you are in production.
Explore secure agent messaging protocols and decentralized protocol choices for deeper guidance on these decisions. When you are ready to implement, the direct agent communication guide walks through concrete setup steps.
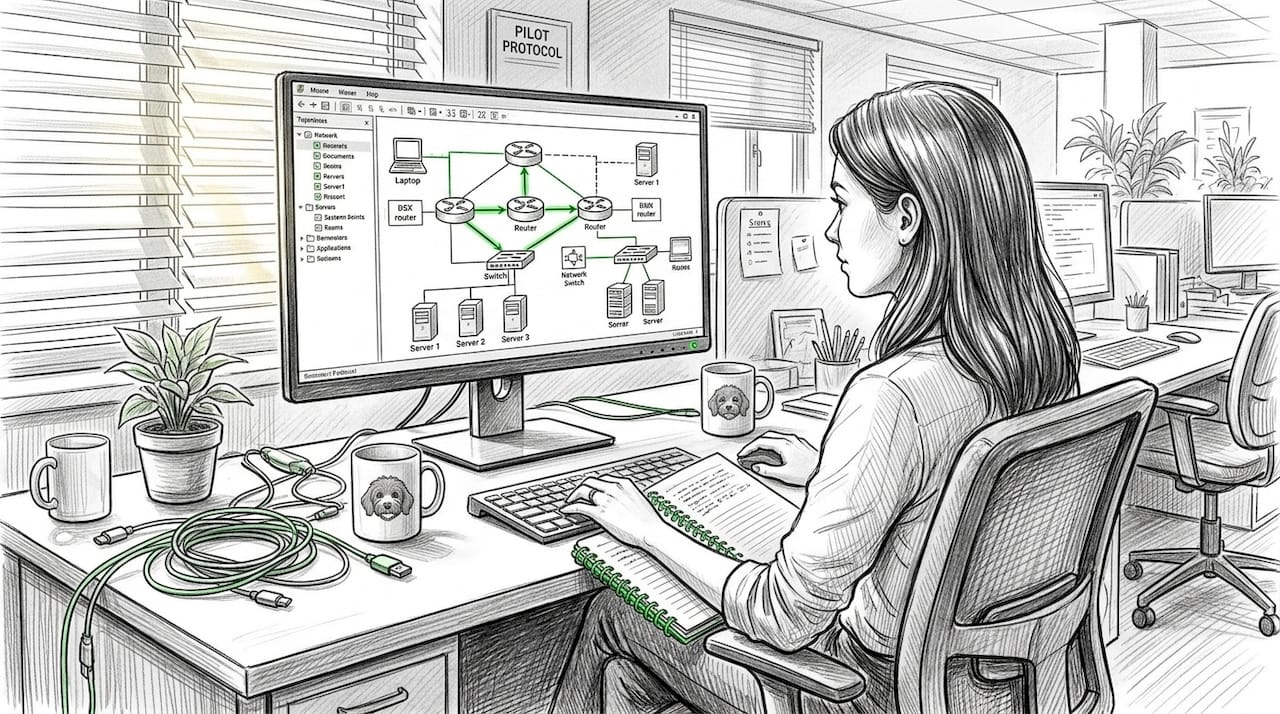
Architectural patterns: Hierarchical vs decentralized security
How you organize your agents structurally is not just a performance decision. It directly determines how well your network survives an attack.
Research on cyberdefense multi-agent systems like cyberSPADE demonstrates that hierarchical architectures using structured messaging platforms balance centralized coordination for strategic decisions with decentralized execution for local tasks, and this balance produces measurably better security outcomes.
The numbers are clear. Hierarchical structures show the lowest performance drop (23.6%) under malicious agents, compared to linear architectures (46.4%) and flat architectures (49.8%). Code generation tasks are the most affected, with a 39.6% drop even in hierarchical setups, which tells you something important: complex task execution is where adversarial agents do the most damage.
| Architecture | Attack tolerance | Latency overhead | Observability | Best for |
|---|---|---|---|---|
| Hierarchical | High (23.6% drop) | Medium | High | Complex orchestration, cyberdefense |
| Linear | Low (46.4% drop) | Low | Medium | Simple pipelines, low-stakes tasks |
| Flat/mesh | Lowest (49.8% drop) | Lowest | Low | Speed-critical, low-trust environments |
Key trade-offs to factor into your architecture decision:
- Hierarchical networks give you a natural place to enforce policies: at the coordinator node that delegates to sub-agents. Observability is highest because every task flows through a choke point.
- Linear pipelines are easy to scale but brittle under attack. A single compromised step can poison every downstream agent.
- Flat mesh networks minimize single points of failure in terms of availability, but they maximize attack surface because every agent communicates with every other agent with no central inspection point.
For most production MAS deployments handling sensitive data or autonomous actions, hierarchical architecture with explicit delegation and audit at each tier is the right starting point. You can always loosen coordination constraints as you build confidence in runtime controls.
Read more about multi-agent hierarchical design and secure MAS architectures to see how these patterns apply to real deployments.
Adaptive defense: Real-world performance and continuous validation
Designing a secure architecture is step one. Keeping it secure under live conditions requires continuous validation. The threat landscape for agent networks evolves faster than most security teams update their controls.
Multi-Agent Reinforcement Learning (MARL) approaches to adaptive defense are proving effective in controlled environments. AI-driven MAS in cyber ranges shows response times of 4.2 seconds on small networks, 5.6 seconds on medium, and 6.1 seconds on large networks. Baseline response times range from 6.5 to 18.4 seconds. RL-based attackers (DQN and Policy Gradient) paired with ML defenders (Random Forest and Autoencoder) produce measurably faster detection and response than static rule-based systems.
Continuous red teaming and challenge/review mechanisms significantly boost resilience. Hierarchical architectures outperform decentralized ones for malicious tolerance, but they require more deliberate observability design to maintain that advantage in practice.
Steps to integrate red-teaming into your MAS security pipeline:
- Define your ACI baseline. Before any red team exercise, measure your current compromise rate and average chain length under controlled conditions. This is your benchmark.
- Run integration attacks. Inject a compromised agent into a non-production copy of your network and observe how far it propagates before detection. Time the response.
- Test replay scenarios. Capture valid A2A messages and replay them to verify your nonce and sequence number controls actually block them.
- Stress-test orchestration hooks. Flood the pub/sub layer with synthetic events and confirm your audit hooks and rate limits hold.
- Iterate on policy rules. Use red team findings to update runtime guardrails, then re-run the ACI measurement to confirm improvement.
Pro Tip: Schedule red team exercises before every major agent version update, not just at deployment. Agent behavior changes with model updates, and your existing policies may no longer match the new output patterns.
For more operational guidance on day-to-day security, the practical P2P security strategies guide covers hands-on steps for keeping agent transfers secure under production conditions.
What most developers overlook in multi-agent security
The most common mistake teams make is treating cryptographic implementation as the finish line. You encrypt the tunnel, you sign the messages, you rotate the keys. Then you declare the system secure and move on. That logic is flawed.
Cryptographic protocols are necessary but not sufficient. The attacks that actually succeed against production MAS deployments do not break encryption. They exploit execution gaps: a prompt that passes transport-layer inspection but carries an injected instruction, an agent that executes a tool call it should have flagged, an audit log that exists but is never reviewed. The protocol does not fail. The observability and enforcement layer fails.
The hidden risk that rarely gets benchmarked is cascading compromise. Teams run unit tests on individual agents and integration tests on pairs. Almost no one runs a full-network adversarial test that measures how far a single compromised agent can spread before the system detects and isolates it. That number, your attack chain length, is your real security posture. It is not visible in code review or static analysis.
Our strong recommendation: design explicitly for compromise visibility. Know your attack chain length before you go to production. Assume some agents will be compromised at some point and build your detection and isolation controls around that assumption rather than trying to make compromise impossible.
Most teams focus on technical implementation because that is measurable and deliverable. Operational resilience, continuous adversarial challenge, and post-compromise forensics feel softer and harder to schedule. They are not. They are the part of the security stack that actually determines whether a breach stays small or becomes a full network takedown.
Explore the deeper agent networking pitfalls resource to see how these blind spots manifest in real architectures and what the practical fixes look like.
Take the next step with secure peer-to-peer agent frameworks
Knowing the right strategies is essential, but deploying them on a network built for AI agents is what makes the difference between theory and production-grade security.

Pilot Protocol is built specifically for this: encrypted peer-to-peer tunnels, mutual trust establishment, NAT traversal, and persistent virtual addresses for every agent in your fleet. You get the audit infrastructure, the direct agent communication layer, and the multi-cloud connectivity that the strategies in this guide require, without building that plumbing yourself. If you are ready to move from architectural planning to deployable infrastructure, peer-to-peer agent networking with Pilot Protocol gives you a direct path to secure, observable, and interoperable agent communication across any cloud or region.
Frequently asked questions
What are the biggest sources of compromise in multi-agent system networks?
Common weaknesses include poor visibility into agent interactions, insufficient runtime policy enforcement, and insecure message passing between autonomous agents. Pre-execution runtime defense that inspects prompts, outputs, and tool calls is the most direct control for preventing cascading compromises.
Which protocol standards are best for secure agent-to-agent communication?
Protocols like A2A and MCP are widely adopted for secure, interoperable messaging in multi-agent systems. The BlockA2A framework adds DID-based authentication and blockchain auditability for higher-assurance deployments.
How can agent networks be tested for security vulnerabilities?
Effective approaches include continuous red teaming, integration attacks, and benchmarking Agent Communication Integrity using metrics like compromise rate and chain length. ACI benchmarks give you measurable targets to improve against each sprint cycle.
Are decentralized or hierarchical agent architectures more secure?
Hierarchical structures typically offer significantly higher malicious tolerance, showing only a 23.6% performance drop compared to 46.4% to 49.8% for linear and flat architectures. Decentralized models reduce latency but are considerably more vulnerable to large-scale compromise under adversarial conditions.